The evolution of Bitcoin wallet security has led to increasingly sophisticated solutions for protecting digital assets, with multisignature (multisig) technology emerging as a cornerstone of advanced cryptocurrency security. This comprehensive analysis explores the fundamental aspects of multisig implementations, their advantages over traditional single-signature wallets, and the critical considerations for long-term storage security. For a deeper look at this topic, see our guide on hardware wallet security models.
Multisig technology represents a significant advancement in Bitcoin’s security architecture by requiring multiple signatures to authorize transactions. Our comprehensive guide on multisig wallet architecture covers this further. This approach fundamentally transforms the security model from a single point of failure to a distributed system of authentication, providing users with unprecedented control over their digital assets. The technology’s implementation in Bitcoin leverages the protocol’s native scripting capabilities, allowing for various configurations such as 2-of-3 or 3-of-5 signature requirements.
The technical foundation of multisig security rests on the careful management of extended public keys (xpubs) and their corresponding private keys. We explore this in detail in our article on Bitcoin multisig security. Each xpub represents a distinct signing authority within the multisig setup, working in concert with others to create a robust security framework. This distributed approach to key management significantly reduces the risk of catastrophic loss while maintaining practical usability for legitimate transactions.
One of the most compelling aspects of multisig technology is its inherent resistance to single-point compromise. Unlike traditional single-signature wallets, where the theft or loss of one private key results in complete loss of funds, multisig setups maintain security even if individual keys are compromised. This characteristic makes multisig particularly valuable for long-term storage solutions and institutional custody arrangements.
The implementation of multisig wallets requires careful consideration of backup procedures and recovery protocols. This topic is explored further in our post on multisig wallet best practices. Users must maintain secure copies of critical wallet data, including xpubs, wallet configuration files, and recovery seeds. The complexity of these requirements necessitates rigorous testing and regular practice of recovery procedures to ensure continued access to funds over time.
Technological longevity represents a crucial consideration in multisig implementation. Bitcoin’s commitment to backward compatibility ensures that properly configured multisig wallets remain accessible despite protocol upgrades and software evolution. This stability provides users with confidence in the long-term viability of their security setup, though regular testing remains essential for operational assurance.
Hardware wallet integration plays a vital role in modern multisig implementations, providing an additional layer of security through air-gapped signing capabilities. You can learn more about this in our resource on hardware wallet multisig setup. The combination of hardware security modules with multisig protocols creates a robust security framework that protects against both physical and digital threats while maintaining practical usability for authorized transactions.
Comparing multisig to distributed single-signature approaches reveals significant advantages in security and key management efficiency. While maintaining multiple single-signature wallets might seem simpler, it actually increases the number of security-critical elements that require protection. Multisig provides superior security with fewer points of potential failure.
Regular testing and validation of recovery procedures emerge as critical operational requirements for maintaining effective multisig security. Users should establish periodic testing protocols to verify their ability to recover funds and execute transactions, ensuring familiarity with recovery procedures and confirming the integrity of backup materials.
The future of Bitcoin security increasingly points toward multisig adoption as users and institutions seek robust solutions for long-term asset protection. The technology’s ability to balance security with usability, combined with its resistance to various attack vectors, positions it as a cornerstone of cryptocurrency security architecture.
Successful implementation of multisig security requires careful attention to documentation and backup procedures. Users must maintain comprehensive records of wallet configurations, including xpubs, fingerprints, and recovery information, stored in secure, geographically distributed locations. This documentation ensures continuity of access across time and changing circumstances.
Looking forward, the continued development of user-friendly multisig implementations and standardized backup procedures will likely accelerate adoption among both individual and institutional users. As the cryptocurrency ecosystem matures, multisig technology stands as a testament to Bitcoin’s capacity for sophisticated security solutions that meet the demands of serious digital asset protection.
Distributing key custody is covered in Multi-Signature Wallet Setup: Security and Portability.
For enhanced protection, consider Bitcoin Custody Security: Multi-Sig Setup Guide.
Multi-signature setups add another security layer — see Multisig Wallet Recovery: Pitfalls and Strategies.
For enhanced protection, consider Multisig Xpub Verification: Security Guide.
For a broader perspective, explore our Bitcoin seed phrase security guide.
Step-by-Step Guide
Implementing an advanced multisig security setup requires methodical planning that accounts for both cryptographic security and real-world operational needs. This guide covers the process from threat modeling through operational verification for a production-grade multisig wallet.
Step 1: Define your threat model. Before selecting any hardware or software, articulate what you are protecting against. Common threats include: device theft (someone physically takes a signing device), remote compromise (malware on a computer used during signing), coercion (someone forces you to sign a transaction), single vendor compromise (a hardware wallet manufacturer ships compromised firmware), and natural disaster (fire, flood destroying backup materials). Your multisig configuration should address each identified threat.
Step 2: Select your quorum and key distribution. Based on your threat model, choose a quorum that provides the security you need without excessive operational burden. A 2-of-3 setup is standard for personal holdings. For higher-value storage, 3-of-5 provides more redundancy. Map each key to a specific physical location and custodian — for example, Key 1 at home (primary signing), Key 2 in a bank safe deposit box (backup), Key 3 with a collaborative custody provider (emergency recovery).
Step 3: Acquire and initialize hardware from diverse manufacturers. Purchase signing devices directly from manufacturers to avoid supply chain tampering. Select at least two different brands — for instance, Coldcard Mk4, Trezor Model T, and Keystone Pro. Initialize each device in a private setting with no cameras or network connections. Generate the seed on-device using the hardware’s built-in random number generator, optionally supplemented with user-provided entropy such as dice rolls.
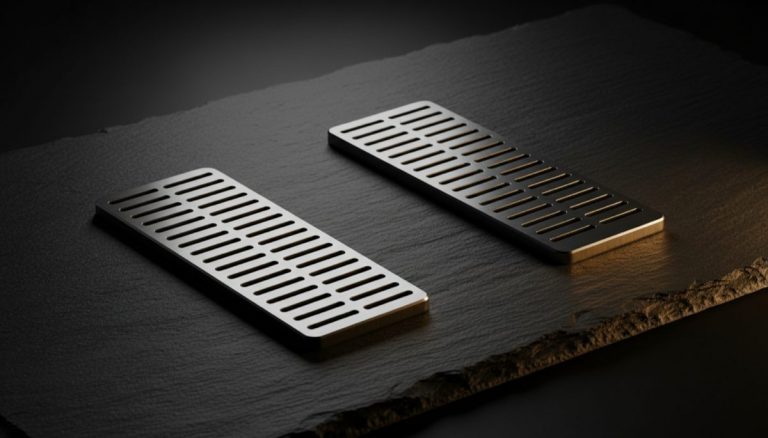
Step 4: Create durable seed backups on metal. Stamp or engrave each seed phrase onto a stainless steel or titanium plate rated for fire resistance above 1,200°C. Verify each backup by comparing it word-by-word against the device’s display. Label each backup with the device’s master key fingerprint (but never the device name or your identity) so you can associate it with the correct key position during recovery without revealing ownership.
Step 5: Build the multisig wallet using a verified coordinator. Download your coordinator software (Sparrow Wallet is recommended for its comprehensive multisig support) from the official source and verify the PGP signature. Import each xpub — using QR codes for air-gapped devices or USB for connected devices. Specify the quorum, script type (use P2WSH for native SegWit multisig), and derivation path (m/48'/0'/0'/2'). Review the generated wallet descriptor.
Step 6: Register the multisig wallet on each hardware device. For devices that support it (Coldcard, Keystone, Jade), import the wallet descriptor or multisig configuration file. This allows each device to independently verify that receive addresses and change addresses belong to the registered wallet. Complete this registration for every device in the quorum before generating any addresses.
Step 7: Verify addresses across all devices. Generate the first five receive addresses in the coordinator software. On each hardware device, use the multisig address verification feature to confirm the same addresses appear. This cross-verification ensures all devices agree on the wallet configuration and prevents address substitution attacks where compromised software could direct funds to an attacker-controlled wallet.
Step 8: Execute a full test cycle and distribute keys. Send a small test amount, then create and sign a spending transaction using the required number of devices. After confirming successful broadcast and on-chain confirmation, distribute the signing devices and seed backups to their designated locations. Document the complete configuration (without private key material) in written instructions stored separately from any single key.
Common Mistakes to Avoid
1. Using the same passphrase across multiple hardware devices. If you apply BIP-39 passphrases to individual keys in your multisig, each device must use a unique passphrase. Reusing the same passphrase across devices reduces the effective security — if the passphrase is compromised, every key protected by it is simultaneously exposed. Either use unique passphrases per device or rely on the multisig quorum itself for security without adding passphrases.
2. Failing to test the complete recovery process. Creating the wallet and testing a transaction is necessary but insufficient. You must also test full wallet recovery: take a blank coordinator installation, import only the wallet descriptor and connect fresh hardware devices restored from your seed backups, then verify you can regenerate the same addresses and sign a transaction. This proves your backups are complete and functional.
3. Keeping all hardware devices in the same room during signing. The security benefit of multisig is partially defeated if all devices are physically co-located, as a single physical intrusion could access multiple keys simultaneously. When possible, sign transactions by bringing partially-signed Bitcoin transactions (PSBTs) to each device’s location rather than bringing all devices together.
4. Not monitoring the multisig wallet for unexpected activity. Set up a watch-only wallet on your primary computer or phone that tracks the multisig addresses. This allows you to detect unexpected incoming or outgoing transactions promptly. Some coordinator software supports this natively — for example, Sparrow can connect to your own Electrum server for private balance and transaction monitoring.
5. Overlooking firmware update procedures for hardware devices. Hardware wallets receive security-critical firmware updates. Establish a procedure for safely updating each device while maintaining your multisig capability — never update all devices simultaneously. Update one device at a time, verify it still functions correctly within the multisig (by generating and verifying an address), and only then proceed to the next device.
Frequently Asked Questions
Does using multisig protect against quantum computing threats?
Multisig does not inherently protect against quantum computing attacks on Bitcoin’s cryptographic primitives. If a quantum computer could break ECDSA (the signature algorithm Bitcoin uses), it could forge signatures for any key — having multiple keys does not help if all of them are individually breakable. However, multisig combined with address non-reuse provides a practical defense: funds sent to a P2WSH address are protected by the hash of the script, not the public keys themselves, until a spending transaction is broadcast. The public keys are only revealed when you spend, at which point a quantum attacker would have the confirmation window to forge signatures. This is the same protection level as singlesig addresses that have never spent.
How should I handle the wallet descriptor for a high-security multisig setup?
The wallet descriptor is less sensitive than seed phrases but more sensitive than individual public addresses. It reveals all xpubs, the quorum structure, and the derivation paths — information that allows full visibility into your balance and transaction history. Store encrypted copies of the descriptor alongside each seed backup (so any seed location has the information needed for wallet reconstruction), and keep one additional copy in a separate secure location. Use GPG or a similar tool to encrypt the descriptor file, with the decryption passphrase documented in your recovery instructions.
Is a 2-of-2 multisig a good configuration?
A 2-of-2 multisig has a critical weakness: losing either key means permanent loss of funds with no recovery path. Unlike 2-of-3 where one key can be lost without consequence, 2-of-2 has zero redundancy. The only practical use case for 2-of-2 is when both signers must actively consent to every transaction (such as a joint account between two parties), and even then, a 2-of-3 with a shared emergency recovery key is generally safer. For personal security, always prefer configurations where the signing threshold is strictly less than the total number of keys.
Can multisig wallets use Taproot (P2TR) script paths?
Bitcoin’s Taproot upgrade (activated November 2021) introduces the ability to encode multisig conditions in script paths while presenting a single public key externally. This improves on-chain privacy because a Taproot multisig spend can appear identical to a singlesig spend when using the key path. However, Taproot multisig tooling is still maturing — not all hardware wallets and coordinators fully support Taproot-based multisig as of early 2026. MuSig2 (a Schnorr-based multi-signature protocol) is particularly promising for key-path spends. Monitor your hardware and software vendors for Taproot multisig support before migrating.
Related Resources
- Multisig Wallet Security: Backup Maps, Privacy, and Key Management — How to organize and protect the backup materials essential for multisig recovery.
- Multisig Xpub Verification: The Critical Security Step — Detailed verification procedures for extended public keys in multisig setups.
- From Single-Signature to Multi-Signature Bitcoin Security — A pathway guide for upgrading from singlesig to multisig custody.
- Multisig Bitcoin Wallet Recovery Protocols — Detailed recovery procedures for various multisig failure scenarios.
- The Complete Guide to Bitcoin Seed Phrase Security — Essential seed management practices for every key in your multisig quorum.