The implementation of secure multisignature (multisig) wallets represents one of the most significant advances in cryptocurrency security, yet it also introduces complex verification challenges that must be carefully addressed. This analysis explores the critical importance of extended public key (xpub) verification in multisig setups and examines the various security considerations that users and developers must navigate.
The foundation of multisig security rests upon the proper verification of extended public keys during wallet setup and operation. When implementing a multisig wallet, users combine multiple private keys, typically stored across different devices or locations, to authorize transactions. This distribution of signing authority creates a robust security model that protects against single points of failure. However, the security benefits of multisig can be compromised if the initial setup process isn’t handled with rigorous attention to xpub verification.
Extended public keys serve as the cornerstone of hierarchical deterministic (HD) wallet structures, enabling the generation of multiple receiving addresses from a single master key. In a multisig context, the accurate verification of these xpubs becomes paramount, as any compromise in this process could lead to catastrophic loss of funds. The verification challenge stems from the need to ensure that the xpubs being used actually correspond to the intended hardware wallets or signing devices.
A sophisticated attack vector exists wherein malicious software could potentially display incorrect xpub information during the wallet setup process. This attack could trick users into creating a multisig wallet where one or more of the signing keys are controlled by an attacker rather than the intended hardware devices. The implications of such an attack are severe – users might believe their funds are secured by multiple independent devices when in reality, an attacker holds one or more of the required keys.
The technical solution to this challenge involves implementing robust verification procedures that establish a trusted path between hardware devices and the user interface. Hardware wallets must be capable of displaying their own xpub information directly on their secure displays, allowing users to verify that the keys being used in the multisig setup match exactly with what their devices are reporting. This verification step cannot be delegated to potentially compromised software running on a computer.
Modern hardware wallet implementations have evolved to address these security considerations through various approaches. Some devices implement dedicated xpub verification features, while others rely on alternative security mechanisms. The key principle remains consistent: users must have a way to verify that the xpubs being used in their multisig setup genuinely correspond to their hardware devices.
Beyond the technical implementation, proper user education plays a crucial role in maintaining multisig security. Users must understand the importance of xpub verification and the specific steps required to perform this verification on their chosen hardware devices. This understanding should extend to recognizing potential attack vectors and following security best practices during wallet setup and operation.
The cryptocurrency industry continues to evolve in its approach to multisig security, with various wallet providers implementing different solutions to the xpub verification challenge. These solutions must balance security requirements with usability considerations, as overly complex verification procedures might lead users to skip crucial security steps.
Looking toward the future, the development of standardized protocols for xpub verification in multisig setups could help ensure consistent security across different hardware wallet implementations. Such standards would need to address not only the technical aspects of verification but also the user interface considerations that make security procedures accessible and practical for users of varying technical expertise.
As cryptocurrency adoption grows and institutional players increasingly rely on multisig solutions for treasury management, the importance of robust xpub verification will only increase. The industry must continue to innovate in this space, developing more sophisticated security measures while maintaining the usability that makes cryptocurrency accessible to a broader audience.
For more on this topic, see our guide on Bitcoin Seed Phrase Security.
For more on this topic, see our guide on Bitcoin Security: Cold vs Hot Wallet Setup. Multi-signature setups add another security layer — see Multisig Bitcoin Backup: Advanced Strategy.
Quorum-based security improves on this — explore Multisig Security Analysis: Advanced Wallet Tech.
Distributing key custody is covered in Singlesig to Multisig Bitcoin Migration.
Quorum-based security improves on this — explore Bitcoin Security: Multi-Sig and Air-Gapped Wallets.
For enhanced protection, consider Multisig Wallet: Security vs Usability.
For enhanced protection, consider Multisig Bitcoin Wallet Recovery Protocols.
For a broader perspective, explore our Bitcoin multisig guide guide.
Step-by-Step Guide
Verifying extended public keys in a multisig wallet setup requires methodical attention to detail. Each step in this process builds upon the previous one, and skipping any verification checkpoint can undermine the security of your entire multisig arrangement. Follow this procedure carefully for each hardware device participating in your multisig quorum.
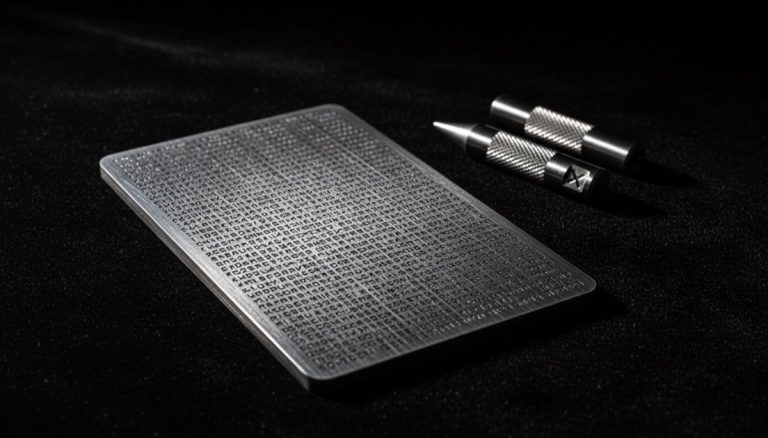
Step 1: Initialize each hardware wallet independently. Before creating the multisig wallet, ensure each hardware device has been initialized with its own unique seed phrase in a secure, offline environment. Power on the device, follow the manufacturer’s setup wizard, and record the seed phrase on a durable medium such as a steel plate. Never generate seeds on a computer or use pre-generated seeds from any source.
Step 2: Export xpubs directly from each hardware device. Navigate to the device’s settings or advanced menu to locate the extended public key export function. On most devices, this is found under Settings → Advanced → Export Xpub or a similar path. The device’s secure display should show the full xpub string, including the derivation path prefix (e.g., m/48'/0'/0'/2' for native SegWit multisig).
Step 3: Record the xpub and master fingerprint from the device display. Write down or photograph the xpub exactly as it appears on the hardware wallet’s trusted screen. Note the master key fingerprint — an 8-character hexadecimal identifier unique to each seed. This fingerprint serves as a quick cross-reference to confirm which device produced which xpub during future verification rounds.
Step 4: Import xpubs into your multisig coordinator software. Using a coordinator application such as Sparrow Wallet, Electrum, or Nunchuk, create a new multisig wallet and import each xpub. The software will display the imported xpubs along with their derivation paths and fingerprints. At this stage, do not yet send any funds to the wallet.
Step 5: Cross-verify each xpub on its corresponding hardware device. This is the critical verification step. For each hardware wallet, use the device’s “verify address” or “show xpub” feature to confirm the xpub displayed in your coordinator software matches exactly what the hardware device shows on its own secure screen. Compare the first 8 and last 8 characters at minimum, though full comparison is recommended.
Step 6: Generate and verify a receive address. After confirming all xpubs, generate the first receive address in the coordinator software. Then, on each hardware device, use the “verify address” feature for multisig to confirm that the device recognizes this address as belonging to the wallet. Each cosigning device should display the same address, confirming they all agree on the wallet configuration.
Step 7: Perform a test transaction. Send a small amount of bitcoin to the verified receive address. Then initiate a spend from the multisig wallet, signing with the required number of devices. This end-to-end test confirms that the wallet is fully operational and that each hardware device can correctly participate in transaction signing. Only after this successful test should you deposit larger amounts.
Step 8: Back up the wallet descriptor and configuration file. Export the multisig wallet descriptor (often in BSMS or JSON format) and store it alongside — but separate from — your seed phrase backups. This descriptor contains all xpubs, derivation paths, and the quorum threshold, and is essential for wallet recovery without re-importing each key manually.
Common Mistakes to Avoid
1. Trusting software-displayed xpubs without hardware verification. The most dangerous mistake is accepting xpubs shown only on your computer screen without confirming them on each hardware device’s secure display. Malware on your computer could substitute an attacker’s xpub, giving them one of the required keys in your multisig quorum. Always verify on the device itself.
2. Skipping the master fingerprint comparison. Each seed generates a unique master key fingerprint. When setting up or restoring a multisig wallet, failing to compare fingerprints between the coordinator software and the hardware device can lead to using the wrong key without realizing it. This mistake often surfaces only when attempting to sign a transaction, at which point funds may already be at risk.
3. Using identical derivation paths across different wallet software. Different coordinator applications may default to different derivation paths for multisig (e.g., m/45' vs m/48'/0'/0'/2'). If you switch coordinator software or attempt recovery using a different application, mismatched derivation paths will generate different xpubs from the same seed, making the wallet appear empty or inaccessible.
4. Failing to back up the wallet configuration file. Many users back up their seed phrases diligently but neglect to store the multisig wallet descriptor. Without this file, reconstructing the wallet requires knowing every xpub, the exact derivation paths, the script type, and the quorum structure — information that is difficult to recover from seeds alone.
5. Not performing a full send-and-spend test before depositing significant funds. Generating an address and receiving bitcoin proves nothing about your ability to spend from the wallet. Hardware devices may accept xpub imports but fail during signing due to firmware bugs, incorrect configurations, or path mismatches. A complete test transaction is the only reliable way to verify end-to-end functionality.
Frequently Asked Questions
What happens if one of my hardware wallets displays a different xpub than expected?
If a hardware wallet displays an xpub that does not match what your coordinator software shows, stop the setup process immediately. This discrepancy could indicate compromised software on your computer, an incorrect derivation path configuration, or in rare cases a firmware issue on the device. Re-download your coordinator software from the official source, verify its signature, and restart the xpub import process. If the mismatch persists after using verified software, check that the derivation path in the coordinator exactly matches the path the hardware device is using for export. Different BIP standards (BIP-45, BIP-48, BIP-87) use different derivation paths, and mixing them will produce different xpubs from the same seed.
Can I verify xpubs if my hardware wallet does not have a dedicated multisig verification feature?
Some older or simpler hardware wallets lack native multisig address verification. In this case, you can still verify the xpub by comparing it character-by-character between the device’s export screen and the coordinator software. However, you will not be able to verify receive addresses on-device for the multisig wallet specifically. This represents a reduced security model — consider upgrading to a device that supports full multisig verification, such as a Coldcard, Keystone, or recent Trezor firmware that includes this capability.
How often should I re-verify my multisig xpubs after initial setup?
Re-verification is recommended whenever you update your coordinator software, upgrade hardware wallet firmware, or restore the wallet configuration on a new computer. As a general practice, performing a quarterly verification — confirming that a test address generated by the coordinator matches what each hardware device displays — provides ongoing assurance that no configuration drift has occurred. This is especially important for large holdings or institutional custody arrangements where the cost of a security failure is high.
Is it safe to share my xpubs with other multisig participants?
Xpubs are less sensitive than private keys, but they are not public information in the same way a single Bitcoin address is. An xpub allows anyone who holds it to derive all past and future addresses for that key’s branch, enabling full visibility into your transaction history and balance. In a collaborative multisig arrangement, sharing xpubs with co-signers is necessary for wallet creation, but you should treat this data as confidential. Transmit xpubs through encrypted channels and avoid storing them in cloud services or email.
Related Resources
- Multisig Wallet Security: Backup Maps and Key Management — A deep dive into organizing and securing the backup materials required for multisig wallets.
- Hardware Wallet Security: Multisig Implementation and Best Practices — How hardware devices integrate with multisig setups and what to look for in a signing device.
- Multisig Wallet Complexity: Common Pitfalls and Recovery Strategies — Practical guidance on navigating the challenges of multisig wallet management.
- Transitioning from Single-Signature to Multisig Bitcoin Wallets — A technical walkthrough for users upgrading their security model from singlesig.
- The Complete Guide to Bitcoin Seed Phrase Security — Essential reading on protecting the seed phrases that underpin every multisig key.