The secure backup of cryptocurrency private keys and seed phrases represents one of the most critical challenges in digital asset security. As the cryptocurrency ecosystem has matured, various approaches to seed backup have emerged, each presenting unique trade-offs between security, usability, and trust requirements. This analysis explores the landscape of seed backup solutions, with a particular focus on Shamir’s Secret Sharing (SSS) and its implementations in modern cryptocurrency security.
The fundamental challenge of seed phrase backup stems from an inherent tension in cryptocurrency security: the need to maintain both redundancy and security simultaneously. A single point of failure in seed storage can result in permanent loss of funds, while multiple copies increase the risk of theft or compromise. This dilemma has driven the development of sophisticated backup solutions that attempt to balance these competing priorities.
Shamir’s Secret Sharing has emerged as a particularly elegant mathematical solution to this challenge. Developed by Adi Shamir in 1979, SSS allows a secret (such as a seed phrase) to be divided into multiple shares, with a configurable threshold required for reconstruction. This approach provides both redundancy and security, as no single share contains enough information to compromise the wallet, while multiple shares can be geographically distributed to prevent physical loss.
The implementation of SSS in cryptocurrency security solutions, however, presents its own set of challenges. While the mathematical foundations of SSS are well-understood and proven, the practical implementation details matter tremendously. Factors such as random number generation, share distribution mechanisms, and the security of the implementation itself all play crucial roles in the overall security of the solution.
Trust considerations become particularly relevant when examining closed-source implementations of SSS. While proprietary solutions may offer polished user interfaces and additional features, their closed nature prevents independent security auditing and verification. This creates a fundamental tension between usability and trustlessness – one of the core principles of cryptocurrency.
Hardware wallet manufacturers have increasingly integrated SSS capabilities directly into their devices, offering a potential middle ground. These implementations benefit from the security guarantees of dedicated hardware but may create vendor lock-in concerns. Users must carefully consider the long-term implications of tying their backup solution to specific hardware providers, particularly given the rapid evolution of the cryptocurrency security landscape.
Open-source alternatives for SSS implementation exist but often require greater technical expertise to implement securely. This highlights a persistent challenge in cryptocurrency security: bridging the gap between theoretical security capabilities and practical, user-friendly implementations that can be safely utilized by a broader audience.
The role of standards and interoperability in seed backup solutions cannot be overlooked. As the cryptocurrency ecosystem continues to mature, the development of standardized approaches to seed backup becomes increasingly important. Standards enable competition among implementations while ensuring long-term accessibility and security.
Looking forward, the evolution of seed backup solutions will likely continue along several parallel tracks. Hardware-based solutions will become more sophisticated, while open-source software implementations will become more user-friendly. The development of quantum-resistant cryptographic techniques may also influence future backup solutions, as the threat model for long-term storage continues to evolve.
The cryptocurrency community faces an ongoing challenge in developing seed backup solutions that maintain the principle of trustlessness while providing the usability required for mainstream adoption. The ideal solution must balance security, redundancy, and ease of use while minimizing trust requirements and avoiding vendor lock-in. As the ecosystem matures, continued innovation in this space will be crucial for the long-term security and accessibility of cryptocurrency assets.
For more on this topic, see our guide on Multi-Signature Wallet Setup: Security and Portability.
Understanding seed security is foundational — read about Seed Phrase Backup: Digital vs Physical.
Proper seed phrase management matters — explore Seed Phrase Memorization: Risks and Tips.
Understanding seed security is foundational — read about Bitcoin Seed Entropy: Randomness Explained.
Proper seed phrase management matters — explore Crypto Wallet Passphrases: Recovery Best Practices.
Proper seed phrase management matters — explore BIP-85 Explained: Derive Multiple Seeds From One.
Step-by-Step Guide to Implementing a Shamir’s Secret Sharing Backup
Shamir’s Secret Sharing (SSS) provides a mathematically robust method for distributing seed phrase backups across multiple locations without any single share being sufficient to compromise your funds. This guide covers the practical implementation using available tools.
Step 1: Determine your threshold configuration. Decide how many total shares to create (N) and how many are required for recovery (M). A common configuration is 2-of-3, meaning three shares are distributed and any two can reconstruct the seed. For higher-value holdings, 3-of-5 provides stronger protection against share loss while maintaining reasonable redundancy.
Step 2: Choose a compatible implementation. The Trezor Model T and Safe 3 natively support SLIP-39, a standardized implementation of Shamir’s Secret Sharing for seed phrase backup. If using another hardware wallet, you can use the open-source shamir39 tool on an air-gapped computer running Tails OS to split a standard BIP39 seed phrase into Shamir shares.
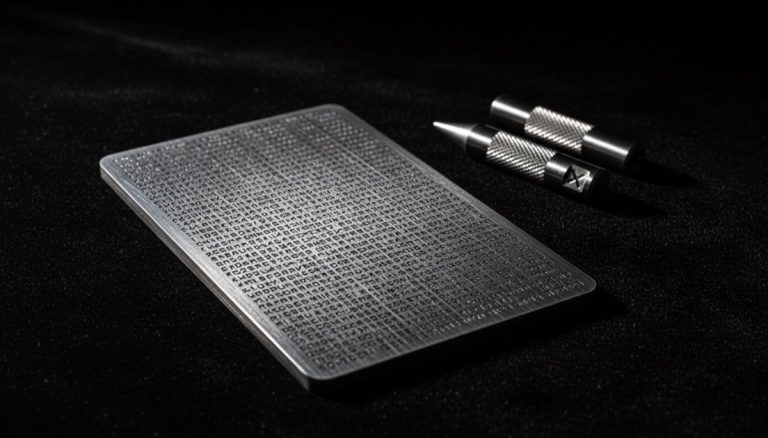
Step 3: Generate shares in a secure environment. On a Trezor with SLIP-39, the device generates shares directly during wallet initialization. Select Advanced Recovery → Shamir Backup and choose your threshold parameters. The device displays each share as a sequence of 20 or 33 words. Write each share on a separate steel plate or archival paper, numbered clearly (Share 1 of 3, Share 2 of 3, etc.).
Step 4: Verify each share independently. After recording all shares, perform a dry-run recovery to confirm each share was recorded accurately. On a Trezor, initiate the recovery process and enter the required threshold of shares. Verify that the recovered wallet produces the expected addresses and fingerprint.
Step 5: Distribute shares to separate geographic locations. Place each share in a different secure location — for example, one in a home safe, one in a bank safety deposit box, and one with a trusted family member. The key principle is that no single location contains enough shares to meet the threshold for recovery.
Step 6: Document the share distribution plan. Create a non-sensitive record that describes where shares are located and the threshold required for recovery, without including the actual share words. Store this document in your estate planning materials. Include instructions for trusted parties on how to locate and combine shares in an emergency.
Step 7: Schedule periodic share verification. Every six to twelve months, visit each share location and verify that the physical medium remains readable and undamaged. Replace any deteriorating backups immediately. For steel plates, check for corrosion or physical damage. For paper backups, verify that ink has not faded.
Step 8: Test the complete recovery workflow annually. Once per year, gather the threshold number of shares and perform a full recovery on a test device. This confirms that the shares produce the correct wallet and that your documented recovery process is accurate and complete.
Common Mistakes to Avoid
Choosing a threshold that is too high or too low. A 1-of-N configuration offers no protection against share theft, as any single share can reconstruct the wallet. Conversely, requiring all N shares (N-of-N) means losing a single share results in permanent fund loss. Choose a threshold that provides a balance between theft resistance and loss tolerance for your specific situation.
Mixing SLIP-39 and BIP39 recovery methods. SLIP-39 shares are not compatible with BIP39 seed phrase recovery, and vice versa. If you generate your wallet using SLIP-39 on a Trezor, you cannot recover it by entering BIP39-style words on a Coldcard. Document which standard your backup uses to avoid confusion during a recovery emergency.
Storing all shares with the same trusted party. Even if shares are in separate envelopes, giving them all to one person or storing them in one building defeats the geographic distribution principle. An attacker who gains access to that single location can collect enough shares to breach your threshold.
Failing to plan for share custodian changes. Trusted parties may become unreachable due to relocation, estrangement, or death. Build a plan for redistributing shares if a custodian becomes unavailable. Periodically verify that all custodians are still accessible and willing to hold their share.
Frequently Asked Questions
Is Shamir’s Secret Sharing more secure than a standard seed phrase backup?
SSS provides superior protection against single-point-of-failure scenarios. A standard seed phrase stored in one location can be compromised by a single theft event or natural disaster. With SSS configured as 2-of-3, an attacker must compromise two separate locations to access your funds, while you can still recover even if one share is destroyed.
Can I add more shares later without changing my wallet?
No, the set of shares is generated together during the initial splitting process. Adding a new share requires regenerating all shares from the original secret, which means collecting the threshold number of existing shares first. For this reason, choose your N and M values carefully at the outset, erring on the side of creating more shares than you think you need.
What happens if I lose one share in a 2-of-3 configuration?
In a 2-of-3 setup, losing one share does not affect your ability to recover the wallet — you still have two remaining shares, which meets the threshold. However, you should immediately generate a new set of three shares from the recovered seed and redistribute them to restore full redundancy. Operating with reduced redundancy leaves you vulnerable to a second share loss.