Understanding the Dark Skippy Attack Vector
The emergence of the Dark Skippy attack has sent shockwaves through the hardware wallet security community, exposing a fundamental vulnerability in how devices handle cryptographic nonce generation. This sophisticated attack represents a paradigm shift in hardware wallet exploitation, demonstrating that even the most security-conscious users can be vulnerable if their device firmware has been compromised.
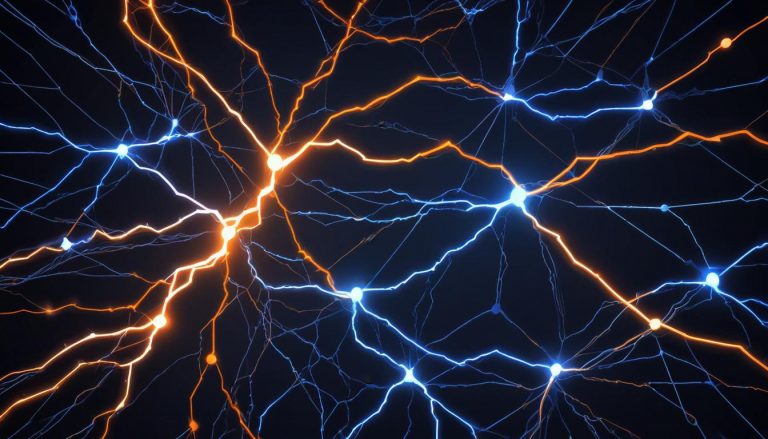
At its core, the Dark Skippy attack targets the nonce generation process during Bitcoin transaction signing. When a hardware wallet signs a transaction, it must generate a unique random number — called a nonce — that protects the private key during the ECDSA signing process. The mathematical security of this process depends entirely on the quality and unpredictability of these nonces. If an attacker can compromise the firmware to generate weak or predictable nonces, they can reverse-engineer the master private key by analyzing just a few transaction signatures on the public blockchain.
What makes Dark Skippy particularly alarming is its stealth. Unlike physical tampering or obvious malware, a compromised firmware generating biased nonces produces transactions that appear perfectly normal on the surface. The signed transactions are valid, the funds move as expected, and there is no immediate indication that anything is wrong — until the attacker has collected enough signatures to extract the master seed. Even additional security measures like BIP39 passphrases may not provide protection, since the attack operates at the cryptographic signing level. This topic is explored further in our post on Bitcoin wallet passphrases.
Supply Chain Attacks: The Hidden Threat
The most realistic pathway for a Dark Skippy-style attack is through supply chain compromise. When a hardware wallet passes through unauthorized hands between the manufacturer and the end user, the risk of firmware tampering increases dramatically. Third-party resellers, unauthorized marketplaces, and even compromised shipping channels all represent potential points where a device could be intercepted and modified.
Supply chain attacks are particularly insidious because they compromise the device before the user ever powers it on. A sophisticated attacker could replace legitimate firmware with a modified version that appears identical in every way — same interface, same features, same behavior — except for subtle modifications to the random number generator. The user would have no way to detect the compromise through normal operation.
The risks extend beyond simple device interception. Advanced supply chain attacks might involve manufacturing counterfeit devices that look identical to legitimate products, complete with packaging, holographic seals, and serial numbers. These counterfeits can contain hardware backdoors at the chip level, compromised secure elements, or firmware that passes superficial verification checks while harboring malicious code.
Purchasing hardware wallets directly from the manufacturer remains the single most important defense against supply chain attacks. When buying directly, you eliminate every middleman who could potentially tamper with the device. Manufacturers like Coldcard, Trezor, and Ledger maintain direct sales channels specifically to minimize this risk. If direct purchase is not possible due to geographic restrictions, using manufacturer-authorized resellers with established reputations is the next best option.
Firmware Verification: Your First Line of Defense
Cryptographic firmware verification represents the most critical technical defense against both Dark Skippy and supply chain attacks. For a deeper look at this topic, see our guide on hardware wallet firmware security. Every reputable hardware wallet manufacturer signs their firmware releases with cryptographic keys, allowing users to verify that the software running on their device has not been modified.
The verification process typically works as follows: the manufacturer publishes firmware files along with their cryptographic signatures. We explore this in detail in our article on Bitcoin cryptographic signatures. When you update or initialize your device, the wallet checks the firmware signature against the manufacturer’s known public key. If the signature does not match — indicating the firmware has been altered — the device should refuse to operate or display a clear warning.
However, not all firmware verification implementations are equal. Some devices perform verification only during updates, while others check firmware integrity every time the device boots. Devices with secure boot processes that verify firmware at every startup provide stronger protection, as they can detect firmware that has been modified after the initial installation.
Open-source firmware designs add another layer of protection by enabling independent security audits. When the entire codebase is publicly available, security researchers worldwide can examine it for vulnerabilities, backdoors, or suspicious nonce generation behavior. Projects with open-source firmware — such as Coldcard and certain Trezor models — benefit from continuous community scrutiny. This transparency makes it significantly harder for any single entity to introduce malicious code without detection.
Secure Element Architecture and Hardware Protection
Modern hardware wallets employ secure elements — specialized microcontrollers designed to resist both physical and electronic attacks. These chips create a hardware-enforced boundary around private key operations, providing protection even if the rest of the device is compromised.
Secure elements are designed to resist a wide range of attack vectors: power analysis attacks that try to infer key material from power consumption patterns, fault injection attacks that introduce errors to bypass security checks, and physical probing attacks that attempt to read data directly from the chip. The implementation quality of these protections varies between manufacturers and chip designs, making it important to evaluate the specific secure element used in any wallet you consider.
However, secure elements are not a silver bullet. The Dark Skippy attack demonstrates that if firmware running on the secure element itself is compromised, the hardware protections become meaningless — the device will faithfully execute malicious code within its secure boundary. This is why firmware verification and supply chain integrity are essential complements to hardware security.
Some manufacturers have taken alternative approaches, arguing that secure elements introduce their own trust assumptions since they typically use proprietary, closed-source designs. These manufacturers instead rely on minimizing the attack surface through air-gapped designs and open-source implementations that can be fully audited. Both approaches have merit, and understanding the specific security model of your chosen wallet is crucial.
Practical Defense Strategies Against Nonce Attacks
Protecting yourself against Dark Skippy and similar nonce-based attacks requires a multi-layered defense strategy that goes beyond any single security measure.
1. Always buy direct from manufacturers. This eliminates the most common supply chain attack vector. If you must use a reseller, verify they are officially authorized by the manufacturer and check the device thoroughly upon receipt.
2. Verify firmware before first use. Download firmware directly from the manufacturer’s official website and verify cryptographic signatures. Never use a device that comes pre-initialized or with a seed phrase already generated — this is a red flag indicating potential tampering. Our comprehensive guide on Bitcoin seed phrase management covers this further.
3. Generate fresh seeds on verified devices. Always generate your seed phrase on a device running verified firmware. If you have any doubt about a device’s integrity, reset it completely and start fresh with a new seed.
4. Use multi-signature setups for high-value storage. Multisig configurations using hardware wallets from different manufacturers provide robust protection against single-device compromise. You can learn more about this in our resource on hardware wallet multisig setup. Even if one device has been affected by a Dark Skippy attack, the attacker cannot steal funds without also compromising the other signing devices.
5. Verify addresses across multiple independent devices. Before sending funds, confirm the receiving address on multiple hardware wallets or through an independent verification method. This helps detect address substitution attacks that might accompany firmware compromise.
6. Monitor for unusual behavior. Stay informed about security advisories from your hardware wallet manufacturer. If a vulnerability like Dark Skippy is discovered, manufacturers typically release patches quickly. Following official channels ensures you receive timely notification of any issues.
The Role of Open Source in Wallet Security
The open-source movement in hardware wallet development plays a crucial role in defending against attacks like Dark Skippy. When firmware source code is publicly available, the security community can audit the nonce generation algorithms, verify the randomness of signature components, and identify any code that could weaken cryptographic operations.
Open-source projects benefit from what security researchers call “many eyes” — the more people who review the code, the more likely it is that vulnerabilities will be discovered and fixed before they can be exploited. This community-driven approach to security has proven effective across the broader software industry and is equally valuable in the hardware wallet space.
Some open-source hardware wallet projects have gone even further, making not just their firmware but their entire hardware designs publicly available. This enables independent verification of manufacturing processes and allows users to build their own devices if they prefer not to trust any manufacturer’s supply chain. While building your own wallet is impractical for most users, the option to do so represents the ultimate expression of trustless verification.
Looking Forward: The Arms Race Continues
The Dark Skippy attack represents just one chapter in an ongoing arms race between hardware wallet security and increasingly sophisticated threats. As the value secured by hardware wallets continues to grow, so does the incentive for attackers to develop new exploitation techniques.
Future defenses may include anti-exfiltration protocols that use deterministic nonce generation schemes, making it mathematically provable that nonces have not been manipulated. Research into these protocols is active, and some wallet manufacturers are already implementing preliminary versions.
The hardware wallet industry must also continue advancing quantum-resistant cryptographic implementations, enhanced firmware attestation mechanisms, and more sophisticated tamper detection systems. For users, the key takeaway remains constant: understand your device’s security model, verify everything you can, maintain strict supply chain hygiene, and never assume that any single security measure is sufficient on its own.
Hardware wallet security is not a destination but an ongoing practice. By staying informed about emerging threats like Dark Skippy, maintaining proper verification procedures, and implementing defense-in-depth strategies, you can significantly reduce your risk and protect your Bitcoin holdings against even the most sophisticated attacks.
Step-by-Step Guide: Verifying Your Hardware Wallet Against Dark Skippy
These steps help you verify that your hardware wallet has not been compromised by a Dark Skippy-style firmware attack, and establish ongoing protection practices.
Step 1: Verify your device’s provenance. Check your purchase records to confirm you bought directly from the manufacturer or an authorized reseller. If the device came from a third-party marketplace (eBay, Amazon third-party sellers, Craigslist), treat it with suspicion. Inspect the packaging for signs of tampering — broken seals, misaligned holographic stickers, or repackaged materials. Coldcard devices include a tamper-evident bag with a unique serial number that can be verified against manufacture records.
Step 2: Verify firmware authenticity. Before trusting any wallet with funds, confirm the firmware is legitimate. On Coldcard: navigate to Advanced/Tools > Upgrade Firmware > Show Version and compare the displayed version and checksum against the values published on coldcard.com/docs/upgrade. On Trezor: open Trezor Suite, connect the device, and check the firmware version under Device Settings — the Suite automatically verifies signatures. On Ledger: open Ledger Live, which performs a genuine check during each connection.
Step 3: Generate a fresh seed on verified firmware. If you have any doubt about your device’s history, factory reset it and generate a new seed phrase. On Coldcard, navigate to Advanced/Tools > Danger Zone > Seed Functions > Destroy Seed, then set up the device fresh. On Trezor, use Device Settings > Wipe Device. Never import a seed from a potentially compromised device into a new one — always generate fresh entropy.
Step 4: Test with a small transaction before loading funds. After setup, send a small amount of Bitcoin to the wallet, then spend from it. This confirms the device can sign valid transactions. While this does not directly detect biased nonces (that requires cryptographic analysis), it verifies basic operation and gives you a signed transaction you could later analyze with specialized tools if a vulnerability is disclosed.
Step 5: Implement ongoing monitoring. Subscribe to your hardware wallet manufacturer’s security advisory channels — email lists, RSS feeds, or verified social media accounts. When a vulnerability is disclosed, the manufacturer will typically release a firmware update within days. Apply security patches promptly. For high-value holdings, consider monitoring Bitcoin security research outlets like the Bitcoin-dev mailing list and security-focused Bitcoin podcasts.
Warning: If a Dark Skippy or similar nonce vulnerability is publicly disclosed for your device’s firmware version, move your funds immediately. Do not wait for a firmware update — the attack can extract your seed from transactions already on the blockchain. Generate a new seed on a verified device (or a different manufacturer’s device) and transfer all funds before the attacker can act.
Common Mistakes to Avoid
Assuming “verified” firmware means permanent safety. Firmware verification confirms the software at the time of verification. It does not protect against future supply chain attacks if the device is physically accessed later, nor does it account for undiscovered vulnerabilities in the verified firmware itself. Treat verification as a snapshot, not a permanent guarantee.
Ignoring firmware updates because “it’s working fine.” Unpatched firmware with known vulnerabilities is an active risk. The Dark Skippy attack demonstrates that a firmware-level exploit can silently extract your seed over time. Each transaction you sign with vulnerable firmware potentially leaks information. Update promptly when security patches are released.
Using a single hardware wallet for all Bitcoin holdings. A single point of failure means a single Dark Skippy-style attack compromises everything. Distribute holdings across multiple wallets from different manufacturers. A 2-of-3 multisig setup using devices from Coldcard, Trezor, and BitBox02 ensures that even if one manufacturer’s firmware is compromised, your funds remain safe.
Buying hardware wallets based solely on price from unauthorized sellers. The discount is not worth the risk. A compromised device sold at a slight markdown can steal everything you ever store on it. The $50-200 you might save by buying from an unauthorized source is insignificant compared to the potential loss.
Frequently Asked Questions
Can Dark Skippy steal my Bitcoin without me noticing?
Yes. That is what makes it particularly dangerous. The compromised firmware produces valid-looking transactions with biased nonces. The Bitcoin moves as expected, and the transaction appears normal on the blockchain. The attacker silently collects signed transactions from the public blockchain and mathematically extracts the master seed after observing enough signatures — as few as two transactions in some attack variants. You would not know anything was wrong until the attacker sweeps all funds.
Does a BIP39 passphrase protect against Dark Skippy?
Not fully. While a passphrase adds complexity, the Dark Skippy attack operates at the nonce generation level during transaction signing. Some variants of the attack can exfiltrate the passphrase-derived key material along with the seed. A passphrase provides better protection against physical seed theft than against firmware-level nonce manipulation. Do not rely on a passphrase alone as a defense against compromised firmware.
Which hardware wallets are immune to Dark Skippy?
No hardware wallet is inherently immune to nonce manipulation attacks if its firmware is compromised. The vulnerability is fundamental to the ECDSA signing process used in Bitcoin. However, wallets with open-source firmware (Coldcard, Trezor) allow community auditing that makes hidden nonce manipulation harder to introduce. Some wallets are implementing anti-exfiltration protocols (like RFC 6979 deterministic nonces with host-side verification) that mathematically prevent nonce bias even in compromised firmware.
Should I stop using my hardware wallet because of Dark Skippy?
No. Dark Skippy requires the firmware to be compromised first — it is not a remote attack. If you bought your device directly from the manufacturer, run verified firmware, and keep it updated, your risk is extremely low. The attack is primarily a concern for devices obtained through untrusted supply chains or those running outdated firmware. Hardware wallets remain the most secure method of storing Bitcoin private keys.
For a broader perspective, explore our Bitcoin seed phrase security guide.
Related Resources
- Hardware Wallet Firmware Updates: Security Best Practices
- Hardware Wallet Multisig Setup Guide
- Side-Channel Attack Risks in Hardware Wallet Security
- Seed Phrase Storage Best Practices
- Cryptographic Signatures in Bitcoin: From ECDSA to Modern Solutions
Dedicated signing devices strengthen your setup — explore Hardware Wallet Buying Guide 2026.
For secure signing practices, see Hardware Wallet Seed Phrase Migration: Step by Step.