The deployment of Bitcoin nodes represents a critical infrastructure component in maintaining the network’s decentralization and security. As the cryptocurrency ecosystem continues to evolve, the choice of operating system and hardware configuration has become increasingly important for node operators. This analysis explores the fundamental considerations and trade-offs involved in establishing and maintaining a secure Bitcoin node infrastructure.
The foundation of any Bitcoin node deployment begins with the selection of an appropriate operating system environment. While mainstream Linux distributions offer robust security features and extensive community support, purpose-built systems designed specifically for cryptocurrency nodes present their own unique advantages and challenges. The primary considerations extend beyond mere functionality to encompass security architecture, update mechanisms, and potential attack vectors.
Traditional Linux distributions like Ubuntu Server or Debian provide a well-understood security model with predictable update cycles and extensive documentation. These systems benefit from decades of hardening in production environments and regular security audits by a global community of developers. The transparency of their development process and the ability to customize security configurations make them particularly attractive for security-conscious node operators.
Purpose-built node operating systems have emerged as an alternative approach, offering streamlined deployment processes and integrated management interfaces. These systems abstract much of the underlying complexity while providing specialized features for cryptocurrency applications. However, this convenience comes with important security considerations, particularly regarding the trust model and attack surface of these more specialized solutions.
The security implications of operating system choice extend beyond the core system to encompass package management, network configuration, and access control mechanisms. Traditional distributions typically implement robust package signing and verification systems, with clear chains of trust extending from package maintainers to end users. This established security infrastructure provides important guarantees about software integrity and authenticity.
When evaluating specialized node operating systems, operators must carefully consider the implications of delegating trust to additional parties. While these systems may offer enhanced usability, they introduce new potential points of failure and security considerations. The relative newness of some solutions means they may not have undergone the same level of security scrutiny as traditional operating systems.
Resource management and system hardening represent another crucial aspect of node deployment. Traditional Linux distributions provide extensive tools and documentation for system hardening, allowing operators to implement defense-in-depth strategies appropriate for their security requirements. This includes capabilities for detailed audit logging, network monitoring, and access control configuration.
Network security considerations play a vital role in node deployment strategy. The choice of operating system impacts available firewall configurations, VPN integration options, and the ability to implement network segregation. Traditional distributions typically offer more flexible networking configurations, while specialized solutions may prioritize ease of use over configurability.
The maintenance lifecycle of the chosen operating system directly affects the long-term security posture of the node. Traditional distributions have well-defined support periods and security update policies, providing predictability for operational planning. Specialized solutions may have different update cycles and support models, requiring careful evaluation of their long-term viability.
The implications of these choices extend to the broader Bitcoin network’s security and decentralization. Each node’s security posture contributes to the overall resilience of the network, making operating system selection an important consideration for the ecosystem as a whole. The balance between security, usability, and maintenance requirements must be carefully weighed against the operator’s technical capabilities and security requirements.
Looking forward, the evolution of both traditional and specialized operating systems will continue to shape the landscape of Bitcoin node deployment. Advances in system security, containerization, and automated management tools will likely influence future deployment strategies. The ongoing development of purpose-built solutions may lead to new security paradigms specifically tailored to cryptocurrency infrastructure.
In conclusion, the selection of an operating system for Bitcoin node deployment requires careful consideration of security architecture, trust models, and operational requirements. While traditional Linux distributions offer proven security models and extensive customization options, purpose-built solutions provide streamlined deployment at the cost of additional trust considerations. The optimal choice depends on the operator’s specific requirements, technical capabilities, and security priorities.
For more on this topic, see our guide on Lightning Node Mobile Integration Guide.
For more on this topic, see our guide on Digital Security for Bitcoin Asset Holders. Full sovereignty starts with your own node — explore Bitcoin Node Operation: Health and Updates.
For more on this topic, see our guide on Hardware Wallet Buying Guide 2026. Verifying transactions yourself requires a node — see Bitcoin Node Software: Core vs Alternatives.
Full sovereignty starts with your own node — explore Bitcoin Wallet-Node Sync: How It Works.
Running your own node strengthens this approach — learn about Listening vs Non-Listening Nodes Explained.
Running your own node strengthens this approach — learn about Bitcoin Node Connectivity: Troubleshooting.
Running your own node strengthens this approach — learn about Bitcoin Node Solutions: Self-Sovereign Setup Guide.
For a broader perspective, explore our running your own Bitcoin node guide.
Step-by-Step Guide
Deploying a production-grade Bitcoin node involves making deliberate architectural decisions at every layer. This guide covers the critical steps from OS installation through full operational readiness.
Step 1: Select and Prepare Your Hardware. For a dedicated Bitcoin node, an Intel NUC, a mini-PC with 8GB+ RAM, or a refurbished enterprise small-form-factor machine provides strong performance at reasonable cost. Pair it with a 2TB NVMe or SATA SSD — the extra capacity above the current ~550GB blockchain provides room for transaction indexing and future growth. Avoid USB-attached drives for production nodes, as they introduce a reliability bottleneck. If using a Raspberry Pi, ensure a quality power supply (3.5A minimum) to prevent corruption from voltage drops.
Step 2: Harden the Operating System. Install Ubuntu Server 22.04 LTS or Debian 12 minimal. During setup, enable full disk encryption (LUKS) to protect blockchain data and wallet files at rest. After installation, disable root login, create a non-root user for node operations, configure SSH key-based authentication (disabling password auth), and install fail2ban to block brute-force SSH attempts. Apply all security updates with sudo apt update && sudo apt upgrade and enable unattended security updates for ongoing patch management.
Step 3: Install and Configure Bitcoin Core. Download the latest Bitcoin Core release from bitcoincore.org. Verify the SHA256 hash and GPG signature before installation. Create a dedicated bitcoin.conf with production settings: server=1 enables RPC; txindex=1 enables full transaction indexing (required for Electrum server); dbcache=2048 allocates 2GB of RAM to the UTXO database cache (adjust based on available RAM); and maxconnections=40 balances network contribution against bandwidth limits.
Step 4: Configure Network Architecture. Decide between clearnet, Tor-only, or hybrid networking. For a Tor-only node, add proxy=127.0.0.1:9050 and listen=1 and bind=127.0.0.1 to bitcoin.conf. For clearnet, forward port 8333 on your router and configure your firewall with ufw allow 8333/tcp. A hybrid approach runs clearnet for performance while adding Tor for privacy — configure onlynet=onion and onlynet=ipv4 together. Set dns=0 when using Tor exclusively to prevent DNS leaks.
Step 5: Deploy an Electrum Server for Wallet Connectivity. Install Fulcrum (high performance, requires 8GB+ RAM) or Electrs (lower resource usage, slower indexing). Point the Electrum server at your Bitcoin Core RPC interface. Fulcrum takes 24-48 hours to build its initial index on an SSD; Electrs can take several days. Once indexed, configure your desktop and mobile wallets (Sparrow, Electrum, BlueWallet) to connect to your Electrum server’s address, typically on port 50001 (TCP) or 50002 (SSL).
Step 6: Add Lightning Network Capability. Install LND or Core Lightning on top of your Bitcoin Core backend. Configure channel database backups, watchtower connections, and appropriate channel sizes based on your expected usage. For LND, set bitcoin.node=bitcoind in lnd.conf to use your local Bitcoin Core instance. Allocate sufficient funds for channel opening transactions and set a reasonable minimum channel size (typically 500,000-2,000,000 sats) to avoid tiny channels with unfavorable fee-to-value ratios.
Step 7: Implement Monitoring and Automated Maintenance. Set up systemd service files for all components with automatic restart policies. Install monitoring tools like Prometheus and Grafana for visual dashboards, or use simpler solutions like node-exporter with ntfy.sh alerts. Configure log rotation for Bitcoin Core, your Electrum server, and Lightning implementation. Create a cron job to check disk space daily and alert when available storage drops below 50GB. Schedule periodic reboots (monthly) during low-usage periods to apply kernel updates.
Common Mistakes to Avoid
1. Under-Provisioning Storage. The Bitcoin blockchain grows by 50-80GB per year, and Electrum server indexes add another 30-100GB depending on the implementation. A 1TB drive that seems spacious during initial setup may fill within 2-3 years. Always provision at least 2TB for a full archival node with Electrum indexing, and monitor disk space actively. Running out of storage causes database corruption that may require a complete re-sync.
2. Setting dbcache Too High or Too Low. The dbcache parameter controls how much RAM Bitcoin Core allocates for the UTXO database cache. During initial block download, a high value (4096 or more) dramatically speeds up synchronization. However, setting it higher than available RAM causes swap thrashing that is far worse than a lower setting. After IBD completes, reduce dbcache to 450-1024 to free RAM for other services like your Electrum server and Lightning implementation.
3. Running All Services as Root. Running Bitcoin Core, Electrum server, or Lightning software as the root user creates a massive security liability. If any service is compromised through a vulnerability, the attacker gains full system access. Create dedicated system users for each service (bitcoin, fulcrum, lnd) with minimal file permissions. Use systemd service files with User= directives to enforce this separation.
4. Neglecting Firewall Configuration. A node with all ports open is an invitation for automated scanning and exploitation. Configure UFW or iptables to allow only the specific ports needed: 8333 (Bitcoin P2P), 50002 (Electrum SSL), 9735 (Lightning P2P), and your SSH port. Deny all other inbound traffic by default. If your node only serves your own wallets, consider restricting Electrum access to your local network or Tor hidden service only.
Frequently Asked Questions
What are the minimum hardware requirements for a Bitcoin full node in 2026?
The absolute minimum is a 2GHz dual-core processor, 4GB RAM, and 600GB SSD storage. This runs Bitcoin Core in pruned mode without additional services. For a practical setup with Electrum server and Lightning, target a quad-core processor, 8GB RAM, and 2TB SSD. The Raspberry Pi 4 (8GB model) with an external SSD meets the minimum requirements but offers limited headroom. For the best experience, an Intel N100-class mini-PC with 16GB RAM provides ample resources for the full stack at approximately $200-300 hardware cost.
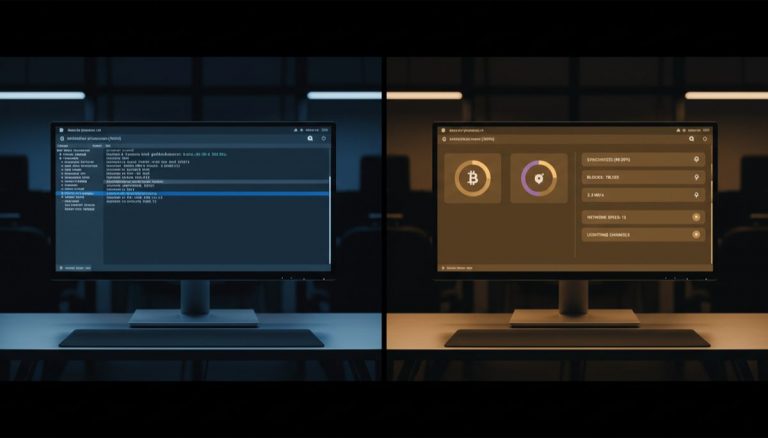
Should I use a plug-and-play node solution or build my own?
Plug-and-play solutions like Umbrel and Start9 offer excellent user experience and work well for users who want a functioning node quickly. Building your own from a bare Linux install gives you deeper understanding, more control, and the ability to troubleshoot issues without relying on the solution’s community. The security tradeoff is nuanced — plug-and-play solutions handle updates and configuration automatically (reducing human error) but add a trust layer in their software stack. For learning and maximum control, build your own. For reliability and convenience, a plug-and-play solution is a solid choice.
How do I securely access my node remotely?
The three primary methods are Tor hidden services, VPN tunnels, and Tailscale/WireGuard mesh networks. Tor is the most private option — it hides your home IP and requires no port forwarding — but connections are slower (500ms-2s latency). WireGuard VPN offers near-native speed with strong encryption but requires port forwarding and exposes your server’s IP to VPN clients. Tailscale provides the easiest setup with no port forwarding required and NAT traversal built in, but routes through their coordination servers for initial handshake. For most users, Tailscale offers the best balance of security and convenience for remote access.
Can I run a Bitcoin node on a VPS or cloud server?
Technically yes, but it undermines the sovereignty principle. A VPS provider can inspect your node’s memory, intercept network traffic, and shut down your instance without notice. If you must use a VPS, choose a provider that accepts Bitcoin payment without KYC and deploy with full disk encryption. Run Bitcoin Core over Tor exclusively to prevent the provider from easily analyzing your traffic. Understand that this setup trusts the VPS provider more than a home setup trusts anyone. For true sovereignty, physical hardware you control is always preferable.
Related Resources
- Why Run Your Own Bitcoin Node — Understand the philosophical and practical motivations behind self-sovereign node operation.
- DIY Bitcoin Node: Build Your Own Setup — Detailed technical analysis of building a node from commodity hardware components.
- Running a Lightning Node: Complete 2026 Guide — Extend your node deployment with Lightning Network capabilities for instant payments.
- Bitcoin Node Security and Decentralization — Explore the trust models and security implications of different node configurations.