The security of digital assets in the cryptocurrency ecosystem fundamentally relies on the proper management of private keys, with seed phrases serving as the critical recovery mechanism for wallet access. As the cryptocurrency landscape evolves, the methods and considerations surrounding seed phrase protection have become increasingly sophisticated, warranting a detailed examination of both traditional and innovative approaches to securing these vital credentials.
The concept of seed phrases, typically consisting of 12 or 24 words selected from a standardized list of 2048 words, represents a significant innovation in cryptocurrency security. These phrases serve as the foundation for generating private keys, effectively becoming the master key to one’s digital assets. The importance of protecting these phrases cannot be overstated, as their compromise would grant complete access to the associated cryptocurrency holdings.
Memory techniques for seed phrase retention draw fascinating parallels with ancient mnemonic practices used by orators and scholars. Modern approaches often leverage the power of narrative and visualization, breaking down the lengthy sequence into manageable chunks and associating them with vivid, interconnected stories. This methodology aligns with established cognitive science principles regarding memory formation and retention.
However, the security implications of seed phrase memorization extend far beyond mere retention capabilities. The practice introduces a complex set of trade-offs between accessibility, security, and human vulnerability. While memorization provides the ultimate in portability and resistance to physical theft or destruction, it also creates unique attack vectors that must be carefully considered in any comprehensive security strategy.
The concept of duress scenarios presents a particularly challenging aspect of seed phrase security. Unlike physical security measures, memorized information becomes vulnerable to coercion techniques, ranging from social engineering to more direct forms of duress. This reality has led to the development of sophisticated countermeasures, including decoy wallets and plausible deniability schemes.
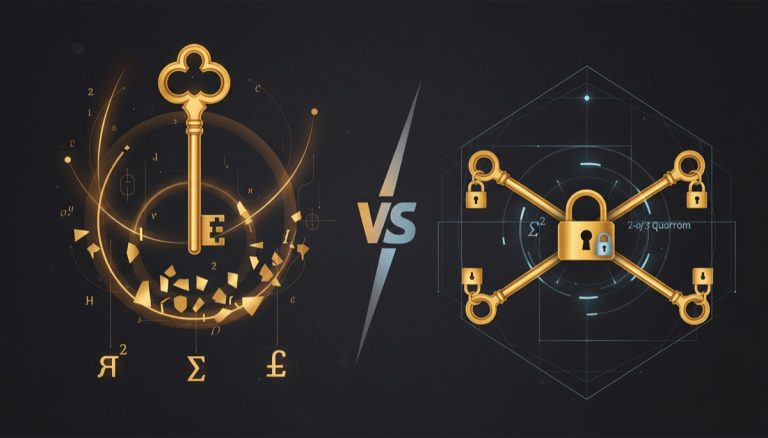
Advanced security implementations often incorporate additional layers of protection beyond the base seed phrase. Passphrases, multi-signature arrangements, and time-locked transactions represent progressive security enhancements that can mitigate the risks associated with seed phrase compromise. These mechanisms effectively transform the seed phrase from a single point of failure into one component of a more robust security framework.
The evolution of seed phrase security practices reflects broader trends in the cryptocurrency ecosystem’s maturation. As the value secured by these phrases has grown, so too has the sophistication of both attack vectors and defense mechanisms. This has led to the development of best practices that often combine multiple security approaches, acknowledging that no single method provides perfect security.
Physical backup solutions, such as steel plates and other durable media, represent an important complement to memorization strategies. These approaches address different threat models and failure modes, suggesting that a comprehensive security strategy might employ both memorization and physical backup components, each serving distinct security objectives.
The future of seed phrase security likely lies in the development of more sophisticated recovery mechanisms that balance security, usability, and resilience. Innovations in social recovery schemes, hardware security modules, and distributed key management systems point toward a future where seed phrase protection becomes more nuanced and adaptable to individual security needs.
Looking forward, the cryptocurrency community continues to grapple with the fundamental tension between security and accessibility. The ongoing evolution of seed phrase protection methods reflects this challenge, as users and developers work to create solutions that provide robust security while remaining practical for everyday use. The future may see the emergence of new paradigms that fundamentally reshape how we approach private key backup and recovery in the cryptocurrency ecosystem.
For more on this topic, see our guide on Bitcoin Cold Storage: Privacy Strategies.
Understanding seed security is foundational — read about Bitcoin Seed Phrase Storage: Best Practices.
Your backup strategy impacts your long-term security — see Bitcoin Seed Entropy: Randomness Explained.
To protect your recovery words, learn about Crypto Seed Backup Solutions: 2026 Review.
Your backup strategy impacts your long-term security — see Seed Phrase Backup: Digital vs Physical.
Proper seed phrase management matters — explore Hardware Wallet Seed Phrase Migration: Step by Step.
Step-by-Step Guide to Secure Seed Phrase Memorization
Memorizing a seed phrase demands a structured approach that accounts for both cognitive limitations and security requirements. The following procedure outlines a method used by experienced Bitcoin holders who choose memorization as one component of their backup strategy.
Step 1: Generate your seed phrase in a secure environment. Boot a dedicated air-gapped device running an open-source operating system. Use a verified wallet application such as Sparrow Wallet or Electrum to generate a fresh 12-word or 24-word BIP39 seed phrase. Never generate seed phrases on an internet-connected device or use online generators.
Step 2: Create a physical backup first. Before attempting memorization, stamp or engrave your seed phrase onto a steel plate using a metal punch set. Store this physical backup in a secure location such as a home safe or bank safety deposit box. This backup serves as your failsafe if memorization fails over time.
Step 3: Break the phrase into groups of three or four words. Cognitive research shows that chunking information into smaller segments significantly improves retention. For a 12-word phrase, create four groups of three words each. Write each group on a separate index card for practice sessions.
Step 4: Build vivid mental associations for each group. Associate each word group with a specific location in your home or a familiar route using the memory palace technique. The more unusual and visual the association, the stronger the memory anchor becomes. For example, if three words relate to nature imagery, picture them arranged in a specific room of your house.
Step 5: Practice retrieval on a daily schedule. During the first week, recite the full phrase from memory at least three times daily. In week two, reduce to twice daily. By week three, practice once daily. After one month, shift to weekly practice sessions. Each session should include writing the phrase down and verifying it against your physical backup.
Step 6: Implement spaced repetition testing. Use increasing intervals between review sessions: 1 day, 3 days, 7 days, 14 days, 30 days, 90 days. If you fail a recall attempt at any interval, reset to the previous interval and work forward again. Track your progress in a private notebook that does not contain the actual seed words.
Step 7: Verify your memorized phrase against the wallet. Periodically restore your wallet on a secure, air-gapped device using only your memorized phrase. Confirm that the derived addresses match your known addresses. This verification confirms both accurate memorization and correct word ordering.
Step 8: Establish a duress protocol. Create a secondary wallet with a small amount of funds accessible through a simple passphrase. Memorize this decoy configuration separately. If compelled to reveal your holdings, this secondary wallet provides plausible deniability while protecting your primary funds.
Common Mistakes to Avoid
Relying solely on memorization without a physical backup. Human memory is fallible, and medical emergencies, head injuries, or prolonged periods of stress can cause recall failures. A steel backup stored in a separate secure location ensures you never lose access to your funds permanently. Treating memorization as your only backup method puts your entire Bitcoin holdings at risk of permanent loss.
Practicing seed phrase recall on insecure devices. Some users type their seed phrase into note-taking apps or text files on their phone or computer to practice. This exposes the phrase to malware, clipboard monitors, and cloud sync services. All verification and practice should occur on air-gapped devices or with pen and paper that is securely destroyed after each session.
Sharing memorization techniques that reveal word patterns. Discussing your mnemonic associations publicly or with untrusted individuals can provide clues about your seed words. Social engineering attacks often begin with seemingly innocent conversations about memory techniques. Keep all details about your memorization approach strictly private.
Neglecting periodic verification over time. Memory degrades without reinforcement. Many users memorize their phrase once and assume it will remain accessible indefinitely. Without scheduled review sessions, critical words or their ordering can become confused, potentially leading to permanent fund loss.
Using predictable word substitutions or patterns. Some users attempt to simplify memorization by choosing seed phrases with recognizable patterns or by repeatedly generating phrases until they find one with familiar words. This practice dramatically reduces the entropy of the seed phrase and weakens its security against brute-force attacks.
Frequently Asked Questions
Can I memorize a 24-word seed phrase reliably?
While 24-word phrases provide stronger security (256 bits of entropy versus 128 bits for 12-word phrases), they are significantly harder to memorize accurately. Most security experts recommend using a 12-word phrase with an additional passphrase for memorization purposes. The passphrase adds entropy while keeping the memorized word count manageable. If you choose to memorize 24 words, plan for a longer learning period and more frequent review sessions.
What happens if I remember the words but forget the exact order?
Word order matters critically in BIP39 seed phrases. Twelve words can be arranged in approximately 479 million different permutations. However, because BIP39 includes a checksum, only a small fraction of permutations produce valid seed phrases. Specialized recovery tools can attempt valid permutations if you know all the words, but this process requires significant computational effort and should only be attempted on an air-gapped device.
Should I memorize my passphrase separately from my seed phrase?
Yes, always treat the seed phrase and passphrase as separate security elements with independent memorization and backup strategies. Store physical backups of each in different geographic locations. This separation ensures that compromise of one element does not grant access to your funds. Use distinct mnemonic techniques for each to avoid confusion between the two.
Is it safe to use a memory palace technique for seed phrases?
Memory palaces are effective for long-term retention, provided you keep the specific associations private. The technique itself does not compromise security — it simply maps words to spatial locations in your mind. The risk arises only if you share or document the specific associations, which could give an attacker clues to reconstruct your phrase.