The evolution of Bitcoin self-custody solutions has given rise to an important focus on air-gapped signing devices, representing a crucial development in cryptocurrency security. These devices serve as a critical bridge between the necessity of transaction signing and the imperative of keeping private keys isolated from potentially compromised networks. This analysis explores the technical considerations, security implications, and practical challenges in implementing air-gapped signing solutions.
The fundamental principle behind air-gapped signing devices stems from a core security maxim: private keys should never be exposed to networked environments. This approach creates a physical security barrier that significantly reduces the attack surface for potential exploits. While commercial hardware wallets implement this concept through specialized hardware, DIY solutions offer unique advantages in terms of transparency, customization, and security verification.
When examining the hardware requirements for air-gapped signing devices, the distinction between networked and non-networked components becomes paramount. Single-board computers (SBCs) with built-in wireless capabilities present a particular challenge, as their networking features represent potential security vulnerabilities. Even when disabled through software, the mere presence of these components raises security concerns due to the theoretical possibility of remote exploitation or firmware-level compromises.
The security architecture of air-gapped signing devices must consider multiple layers of potential vulnerability. Hardware-level security begins with the physical components themselves, where the presence or absence of networking capabilities represents the first line of defense. This extends beyond mere wireless connectivity to encompass all potential communication channels, including Bluetooth, NFC, and other radio frequencies that could theoretically be exploited for data exfiltration.
Software-based solutions for disabling network interfaces present a complex security trade-off. While software controls can effectively disable communication interfaces in normal operation, they rely on the integrity of the operating system and firmware. This creates a dependency chain that could potentially be compromised through sophisticated attacks. The principle of defense in depth suggests that hardware-level isolation provides stronger security guarantees than software-based controls.
Storage Media for Air-Gapped Devices
The role of removable storage in hardware wallet and DIY signing systems extends far beyond simple data retention. These components serve as crucial bridges between air-gapped devices and connected systems, enabling secure transaction signing via PSBTs while maintaining critical security boundaries. MicroSD cards are the most common medium, and their reliability directly impacts custody security.
Industrial-grade storage media typically incorporates several enhanced features compared to consumer variants: improved temperature tolerance, better vibration resistance, enhanced write endurance, and more robust error correction capabilities. While the specific storage requirements for signing devices tend to be modest – even complex multi-signature setups require minimal space – reliability and compatibility are more important than capacity.
Compatibility considerations extend beyond simple physical form factors. File system support, partition schemes, and low-level storage protocols all play crucial roles in ensuring seamless integration. Most modern hardware wallets implement robust compatibility layers, but DIY builders should verify support for their chosen media and file system format.
Supply Chain Security and Component Sourcing
Supply chain security represents a critical consideration in the implementation of air-gapped signing devices. Pre-assembled units, while convenient, introduce potential vectors for compromise through modified hardware or firmware. The security implications extend beyond the device itself to encompass the entire chain of custody from manufacturing to deployment.
The challenge of component availability adds another layer of complexity. The scarcity of specific hardware components forces considerations of alternative approaches, each with its own security implications. This scarcity has led to the emergence of pre-assembled solutions, which introduce additional trust considerations. When sourcing components for DIY builds, purchasing directly from manufacturers or authorized distributors minimizes the risk of tampered parts.
Complete System Architecture
The implementation of air-gapped signing solutions requires careful consideration of the complete system architecture. This includes not only the primary computing unit but also peripheral components such as displays, input devices, and power supplies. Each component must be evaluated for potential security implications, with particular attention to any features that could compromise the air-gap integrity. Users must also consider secure storage of backup devices, protection against environmental factors, and protocols for media replacement.
Looking forward, the development of air-gapped signing solutions continues to evolve alongside advances in hardware security. The trend toward open-source hardware and software solutions provides opportunities for community verification and security auditing, while also enabling customization for specific security requirements. The future of secure transaction signing likely lies in a combination of hardware-level security features and verifiable open-source implementations.
Hardware wallet users should also read Hardware Wallet Buying Guide 2026.
For secure signing practices, see Hardware Wallets and Node Connectivity: Setup Guide.
Physical device security plays a key role — learn about Dark Skippy Attack: Is Your Hardware Wallet Safe?.
Dedicated signing devices strengthen your setup — explore Hardware Wallet Migration: Script Types.
For secure signing practices, see Hardware Wallet Seed Phrase Migration: Step by Step.
Physical device security plays a key role — learn about Hardware Wallet Side-Channel Attack Risks.
To protect your recovery words, learn about Bitcoin Seed Phrase Security.
For enhanced protection, consider Bitcoin Multisig Security: Key Challenges.
Distributing key custody is covered in MultiSig Backup Maps: Protect Keys and Privacy.
Full sovereignty starts with your own node — explore Bitcoin Node and Infrastructure Choice Guide.
Verifying transactions yourself requires a node — see Bitcoin Node Network Discovery and Access.
Broader security architecture matters — review Bitcoin Security: Cold vs Hot Wallet Setup.
Step-by-Step Guide to Building a DIY Bitcoin Signing Device
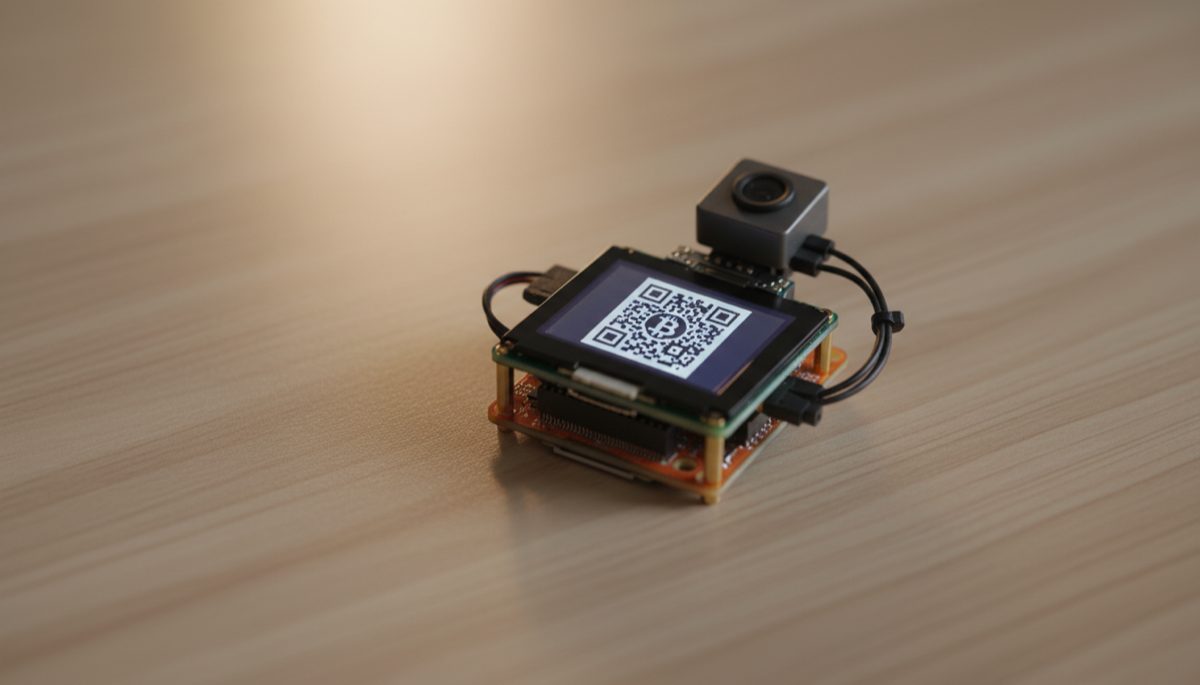
Building your own Bitcoin signing device from open-source components eliminates supply chain risks and gives you full control over every hardware and software component. This guide covers a SeedSigner build using commodity hardware.
Step 1: Source the required components. Purchase a Raspberry Pi Zero 1.3 (the version without WiFi or Bluetooth), a Waveshare 1.3-inch LCD HAT (240×240 pixels), a Pi Zero-compatible camera module, and a microSD card (8GB or larger, industrial-grade preferred). Buy the Raspberry Pi directly from an authorized distributor to minimize supply chain tampering risk. The Pi Zero 1.3 is specifically chosen because it lacks wireless hardware at the circuit level.
Step 2: Download and verify the SeedSigner firmware. Visit the official SeedSigner GitHub repository and download the latest release image file. Verify the download’s SHA-256 hash against the published hash in the release notes. For additional assurance, verify the GPG signature of the release if available. This verification confirms the firmware has not been modified in transit.
Step 3: Flash the firmware to the microSD card. Use Balena Etcher or dd on Linux to write the SeedSigner image to your microSD card. On Linux, the command is: sudo dd bs=4M if=seedsigner_image.img of=/dev/sdX conv=fsync status=progress, where /dev/sdX is your microSD card device. After flashing, eject the card properly to ensure all data is written.
Step 4: Assemble the hardware. Connect the LCD HAT to the Pi Zero’s GPIO header pins. Attach the camera module to the Pi Zero’s camera ribbon cable connector, ensuring the cable is seated firmly and oriented correctly (contacts facing the board). Optionally, mount the assembled components in a 3D-printed enclosure — STL files are available in the SeedSigner repository.
Step 5: Power on and verify operation. Insert the prepared microSD card and connect power via a USB power bank or battery pack. The SeedSigner splash screen should appear on the LCD within a few seconds. Navigate the menus using the HAT’s joystick and buttons to confirm all input controls function correctly. Test the camera by scanning a sample QR code.
Step 6: Generate or import a seed phrase. SeedSigner can generate a new seed phrase using entropy from the camera (photographing random objects) combined with the device’s hardware random number generator. Alternatively, you can import an existing seed phrase by entering each word manually using the on-screen keyboard. After import, verify the wallet fingerprint matches your records.
Step 7: Export the public key to your wallet coordinator. Use SeedSigner’s QR code export function to display your wallet’s xpub as a series of animated QR codes. Scan these codes with Sparrow Wallet on your computer to create a watch-only wallet. This links your coordinator software to the signing device without ever exposing private keys to a networked device.
Step 8: Test the complete signing workflow. Create a test transaction in Sparrow Wallet, export it as an animated QR code, scan it with SeedSigner’s camera, review and sign on the device, then scan the signed PSBT QR code back into Sparrow for broadcasting. Perform this end-to-end test with a small amount of bitcoin before relying on the device for significant holdings.
Common Mistakes to Avoid
Using a Raspberry Pi with built-in WiFi or Bluetooth. The Pi Zero W, Pi Zero 2 W, Pi 3, and Pi 4 all include wireless hardware that creates potential attack vectors even when disabled in software. Firmware-level exploits could theoretically re-enable wireless interfaces. Only the Pi Zero 1.3 (non-W version) physically lacks wireless components, providing hardware-guaranteed air-gap integrity.
Purchasing components from unverified marketplace sellers. Third-party sellers on Amazon, eBay, or AliExpress may ship counterfeit or pre-modified components. A tampered Pi Zero could contain additional circuitry for data exfiltration. Buy from authorized distributors listed on the Raspberry Pi Foundation website or directly from the manufacturer.
Skipping firmware signature verification. Running unverified firmware on your signing device defeats the purpose of a DIY build. An attacker who compromises the firmware download could insert code that leaks your seed phrase through subtle means — for example, biasing the nonce in transaction signatures to encode key material that can be extracted from the blockchain.
Storing the seed phrase on the microSD card. SeedSigner is designed as a stateless signing device — it does not store seed phrases between sessions. This is a feature, not a limitation. You must enter your seed phrase each time you use the device. Never modify the software to store keys on the microSD card, as this would transform a secure signing device into a theft target.
Frequently Asked Questions
How does SeedSigner compare to commercial hardware wallets?
SeedSigner provides comparable signing security for on-chain Bitcoin transactions at a fraction of the cost (approximately $50 in components versus $150-$300 for commercial devices). The tradeoff is usability — SeedSigner requires manual seed entry each session and has a smaller screen. Commercial devices like Coldcard offer additional features such as persistent key storage in a secure element, NFC communication, and built-in keyboard. SeedSigner excels as a secondary signing device in multi-signature configurations.
Can I use SeedSigner as my only signing device?
Yes, SeedSigner functions as a complete signing device. However, its stateless design means you must enter your full seed phrase each time you sign a transaction, which adds time and introduces the risk of entry errors. For daily use, many users prefer a commercial hardware wallet for convenience and reserve SeedSigner as a backup signing device or as one key in a multi-signature quorum.
What maintenance does a DIY signing device require?
Check for firmware updates on the SeedSigner GitHub repository monthly. When updates are available, download the new image, verify its signature, reflash the microSD card, and test the device. Replace the microSD card annually or if you notice any read/write errors. Keep the camera lens clean for reliable QR code scanning. Store the assembled device in a protective case when not in use.