The evolution of Bitcoin wallet security has led to sophisticated solutions that balance accessibility with robust protection mechanisms. Among these innovations, multisignature (multisig) wallet technology stands as a cornerstone of modern Bitcoin security architecture, offering users unprecedented control over their digital assets while maintaining practical usability. Our comprehensive guide on multisig wallet architecture covers this further.
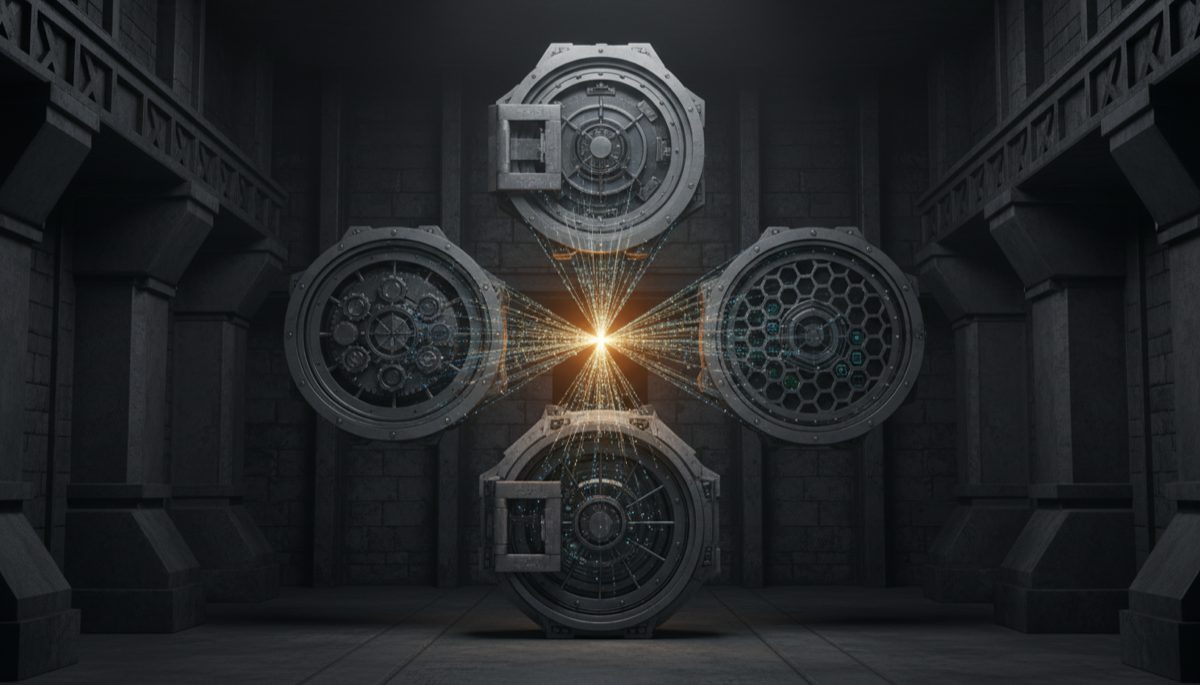
The fundamental principle behind multisignature technology lies in its distributed security model. Rather than relying on a single point of failure, multisig wallets require multiple independent signatures to authorize transactions, typically implementing an M-of-N scheme where M signatures are required from a total of N possible keys. We explore this in detail in our article on multisig wallet best practices. This architecture provides remarkable resilience against both external threats and single-point vulnerabilities.
In the context of personal Bitcoin security, the implementation of multisig solutions represents a significant advancement over traditional single-signature wallets. The ability to distribute signing authority across multiple devices or locations creates a security framework that remains robust even if individual components are compromised. This distributed approach effectively mitigates risks associated with device theft, hardware failure, or physical security breaches.
Modern multisig wallet implementations incorporate sophisticated key management systems that allow users to maintain control over their assets even in worst-case scenarios. The concept of wallet recovery becomes particularly important in this context, as proper backup procedures ensure that users can reconstruct their wallets using various combinations of their original keys. This recovery capability depends critically on maintaining accurate records of crucial wallet configuration details, including derivation paths and extended public keys (xpubs). You can learn more about this in our resource on HD wallet key derivation.
The technical implementation of multisig wallets involves several critical components that users must understand and manage. Extended public keys serve as the foundation for address generation, while derivation paths ensure consistent access to funds across different wallet software. This topic is explored further in our post on HD wallet key management. The importance of maintaining secure backups of these configuration details cannot be overstated, as they form the basis for wallet recovery procedures.
When implementing a multisig security strategy, users must carefully consider their specific threat model and usage requirements. For a deeper look at this topic, see our guide on Bitcoin multisig security. The selection of appropriate key storage locations, backup procedures, and signing quorum requirements should align with individual security needs while maintaining practical usability. This balance between security and convenience represents a crucial consideration in multisig wallet design.
The ecosystem of Bitcoin wallet software continues to evolve, with various implementations offering different approaches to multisig security. Open-source solutions have emerged as particularly important in this space, as they allow for community review and validation of security implementations. The transparency of open-source software provides users with additional confidence in the security of their chosen wallet solution.
Looking toward the future, the continued development of multisig technology promises even more sophisticated security solutions. Innovations in key management, backup procedures, and user interfaces will likely make these advanced security features increasingly accessible to a broader range of Bitcoin users. The integration of hardware security modules and advanced cryptographic techniques may further enhance the security properties of multisig implementations.
The adoption of multisig security represents a crucial step in the maturation of Bitcoin as a financial system. As users increasingly recognize the importance of robust security measures, the role of multisig technology in protecting digital assets will likely continue to grow. This evolution reflects the broader development of Bitcoin’s security infrastructure and its progression toward more sophisticated protection mechanisms.
Step-by-Step Guide
Setting up a multisig wallet requires careful planning and execution across multiple hardware devices and a coordinator application. Follow these steps to create a robust 2-of-3 multisig configuration — the most popular setup for personal Bitcoin security.
Step 1: Acquire Three Hardware Wallets from Different Manufacturers. Purchase one Coldcard, one Trezor (Model T or Safe 3), and one Foundation Passport — or any three hardware wallets from different vendors. Using different manufacturers ensures that a firmware vulnerability in one brand does not compromise your entire multisig quorum. Order directly from each manufacturer’s official website to reduce supply-chain risk. When the devices arrive, verify tamper-evident seals and packaging before powering them on.
Step 2: Initialize Each Hardware Wallet Independently. Power on each device one at a time, generate a new 24-word seed phrase on the device itself, and record the seed phrase on a metal backup plate. Do not generate seed phrases on a computer or phone. Each device should produce its own unique seed phrase without input from the others. After recording each seed phrase, verify it by completing the device’s built-in recovery check (most hardware wallets prompt you to confirm specific words). Label each metal backup clearly: “Key 1 — Coldcard,” “Key 2 — Trezor,” “Key 3 — Passport.”
Step 3: Export Extended Public Keys from Each Device. Using each hardware wallet’s export function, extract the extended public key (xpub) for the multisig derivation path. On Coldcard, use the “Export XPUB” option to microSD. On Trezor, connect to Sparrow Wallet and it will read the xpub automatically. On Passport, use the QR export function. You need all three xpubs to construct the multisig wallet descriptor, which defines which keys participate and how many signatures are required.
Step 4: Create the Multisig Wallet in Sparrow. Open Sparrow Wallet on your dedicated Bitcoin machine (connected to your own node). Select File → New Wallet, name it, and choose “Multi Signature” as the policy type. Set the quorum to 2-of-3. Add each of the three xpubs as a keystore — for Coldcard, import from the microSD file; for Trezor, connect via USB; for Passport, scan the QR code. Once all three keystores are added, Sparrow generates the wallet descriptor and displays the first receiving address. Verify this address on at least two of the hardware wallets to confirm they all agree on the wallet structure.
Step 5: Back Up the Wallet Descriptor. The wallet descriptor contains the derivation paths, xpubs, and quorum configuration needed to reconstruct the wallet. Without it, recovering a multisig wallet from seed phrases alone requires manually figuring out the correct combination of derivation paths and script type — a difficult and error-prone process. Export the descriptor from Sparrow (File → Export Wallet → Output Descriptor) and store copies alongside each seed phrase backup. Each storage location should contain one seed phrase plus the full wallet descriptor.
Step 6: Fund the Wallet and Verify the Signing Flow. Send a small test amount to the wallet’s first receiving address. Once confirmed, create a transaction spending a portion of those funds back to another address you control. Sparrow will construct a Partially Signed Bitcoin Transaction (PSBT). Sign the PSBT with any two of your three hardware wallets — this proves the 2-of-3 quorum works. Verify the transaction details on each hardware wallet’s screen before approving. Once two signatures are collected, Sparrow broadcasts the fully signed transaction.
Step 7: Distribute Keys to Separate Physical Locations. Store each hardware wallet and its associated metal seed backup in a different physical location — for example, your home safe, a bank safe deposit box, and a trusted family member’s secure storage. The 2-of-3 configuration means you can always access your funds with any two of the three keys, while an attacker who compromises any single location cannot spend your bitcoin. Include a copy of the wallet descriptor at each location so that recovery is possible from any two sites.
Common Mistakes to Avoid
Multisig setups are more complex than single-signature wallets, and the added complexity introduces its own category of errors. These mistakes are the most frequently encountered and the most consequential.
1. Using Multiple Keys from the Same Hardware Wallet Brand. A 2-of-3 multisig where all three keys are stored on Coldcard devices provides geographic distribution but not vendor diversity. A firmware bug or vulnerability specific to Coldcard would compromise all three signing devices simultaneously. Always use hardware wallets from at least two different manufacturers to ensure that a single-vendor exploit cannot bypass your quorum.
2. Failing to Back Up the Wallet Descriptor. This is the most common and most devastating multisig mistake. With three seed phrases but no descriptor, you must guess the correct derivation paths, script type (P2SH, P2WSH, P2SH-P2WSH), and the exact order of xpubs in the multisig configuration. Many combinations are possible, and trial-and-error recovery can take days or fail entirely if you do not know the original parameters. Always export and back up the output descriptor alongside every seed phrase.
3. Storing All Seed Phrases in the Same Location. If all three seed phrase backups sit in the same safe, a single burglary, fire, or flood eliminates all of them — and your entire multisig security. The whole point of multisig is distributing trust across multiple locations. Each seed phrase should be in a geographically separate, physically secure location. The wallet descriptor can be stored with each seed since it does not enable spending without the seed phrases.
4. Not Testing the Full Signing and Recovery Flow Before Funding. Load a small amount into the multisig wallet and execute a complete send using two of your three devices before depositing significant funds. Also test recovery: wipe one device, restore it from its seed phrase, re-import the wallet descriptor, and confirm you can still sign transactions. Discovering a configuration error after depositing your life savings is far more stressful than discovering it with a test amount.
5. Using Multisig for Spending Wallets. Multisig adds signing friction — you need two devices in two locations every time you want to send bitcoin. This is ideal for long-term cold storage that you rarely touch, but impractical for daily spending. Maintain a separate single-signature wallet (or Lightning wallet) for regular transactions, and keep your multisig vault for savings that you access infrequently. Moving funds from multisig to spending wallet can be done in planned batches.
Frequently Asked Questions
What is the difference between 2-of-3 and 3-of-5 multisig?
In a 2-of-3 setup, you have three keys and need any two to sign a transaction. This provides redundancy (you can lose one key and still access funds) and security (an attacker needs two keys). In a 3-of-5 setup, you have five keys and need any three. This provides greater redundancy (you can lose two keys) and higher security (an attacker needs three keys), but at the cost of more complexity: five hardware wallets, five seed backups, five physical storage locations, and a more complex signing workflow. For personal use, 2-of-3 offers the best balance of security and practicality. Institutions or high-net-worth individuals managing large amounts may benefit from 3-of-5.
Can I use different wallet software for my multisig instead of Sparrow?
Yes. Multisig wallets are defined by a standard output descriptor that any compatible software can import. Nunchuk, Electrum, Caravan (by Unchained Capital), and BlueWallet all support multisig. You can create the wallet in Sparrow and import the same descriptor into Nunchuk as a backup coordination tool. The hardware wallets sign PSBTs (Partially Signed Bitcoin Transactions), which are a standardized format — any coordinator software that supports PSBTs can work with your signing devices. Using two different coordinator applications provides redundancy if one has a software bug.
What happens if one of my hardware wallet manufacturers goes out of business?
Your seed phrases and wallet descriptor are all you need to maintain access. If Coldcard ceases to exist, you can restore that seed phrase on any BIP39-compatible device (Trezor, Passport, Keystone, or even a software wallet like Electrum). The multisig wallet descriptor specifies the derivation path and script type, which any compatible wallet can replicate. This is why backing up the descriptor is critical — it contains the configuration that makes the seeds work together. Your multisig is not locked to any specific hardware brand.
Is multisig necessary if I use a hardware wallet with a passphrase?
A passphrase (sometimes called the “25th word”) adds a layer of protection to a single-signature wallet by deriving a completely different set of keys from the same seed phrase. It protects against physical theft of the seed phrase — without the passphrase, the thief accesses a decoy wallet rather than your real holdings. However, a passphrase is still a single point of failure: if you forget it, your funds are permanently inaccessible. Multisig provides redundancy that a passphrase cannot — you can lose an entire key and still recover. For significant holdings, multisig is the stronger option. A passphrase on top of multisig keys adds even more protection, but also increases the complexity of your backup requirements.