The intersection of blockchain technology, digital identity systems, and societal transformation represents one of the most significant technological and social developments of our time. As we stand at this crucial juncture, it becomes increasingly important to understand how these technologies are reshaping fundamental aspects of human interaction, financial systems, and personal sovereignty.
The emergence of blockchain technology, particularly through Bitcoin’s introduction in 2009, marked the beginning of a profound shift in how we conceptualize money, value transfer, and digital interactions. This technological revolution has expanded far beyond its initial cryptocurrency applications, now touching virtually every aspect of digital life and raising important questions about privacy, security, and individual autonomy in an increasingly connected world.
The concept of digital identity stands as both a promise and a potential threat in this evolving landscape. While blockchain technology offers unprecedented opportunities for secure, self-sovereign identity management, the same technical capabilities could be leveraged to create sophisticated surveillance and control mechanisms. For a deeper look at this topic, see our guide on self-sovereign Bitcoin node operation. This duality presents a critical challenge for society: how to harness the benefits of digital innovation while preserving fundamental human rights and freedoms.
Blockchain’s role in this transformation extends far beyond its original financial applications. The technology’s core attributes – decentralization, immutability, and transparency – provide a foundation for reimagining how individuals interact with institutions, governments, and each other. These characteristics make blockchain particularly suited for creating robust digital identity systems that could potentially replace traditional identification methods.
However, the implementation of digital identity systems raises significant concerns about privacy and control. While blockchain-based solutions offer enhanced security and user autonomy, there’s a risk that these systems could be co-opted to create more sophisticated forms of surveillance and social control. The challenge lies in developing frameworks that protect individual privacy while enabling necessary social and economic functions.
Bitcoin, as the first and most successful implementation of blockchain technology, offers important lessons for navigating these challenges. Its decentralized nature and emphasis on individual sovereignty provide a model for how digital systems can be designed to enhance rather than restrict personal freedom. The Bitcoin network demonstrates that it’s possible to create robust, secure systems that operate without central control or oversight.
The potential integration of digital identity systems with cryptocurrency networks presents both opportunities and risks. On one hand, such integration could enable more efficient, secure financial services and reduce fraud. On the other hand, it could potentially compromise the pseudonymous nature of cryptocurrency transactions that many users value. Finding the right balance between convenience and privacy remains a central challenge.
Looking forward, the development of these technologies will likely continue to accelerate, making it crucial to establish appropriate governance frameworks and technical standards. These frameworks must prioritize individual rights while enabling the benefits of digital innovation. The role of open-source development and community governance, as exemplified by Bitcoin, could serve as a model for future digital identity solutions.
The implications of these developments extend far beyond technical considerations. They touch on fundamental questions about the nature of privacy, freedom, and human rights in the digital age. As these systems evolve, maintaining a balance between technological progress and individual sovereignty will become increasingly important.
In conclusion, the convergence of blockchain technology, digital identity systems, and cryptocurrency represents a pivotal moment in human history. The decisions made today about how these technologies are implemented and governed will have lasting implications for future generations. Success will require careful consideration of both the technical and social aspects of these systems, ensuring that innovation serves to enhance rather than diminish human freedom and dignity.
For more on this topic, see our guide on Bitcoin Node Sync: Solve Technical Challenges.
For more on this topic, see our guide on Lightning Network Liquidity: Channel Guide. Maintaining on-chain privacy is relevant here — read P2P Bitcoin Trading: Privacy Guide.
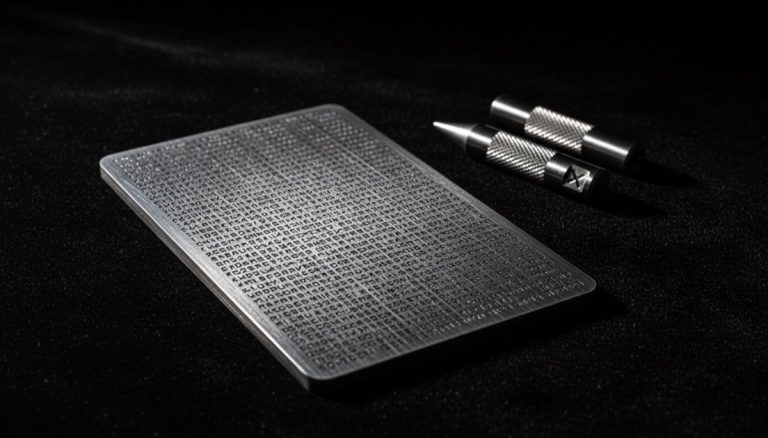
For more on this topic, see our guide on Bitcoin Seed Phrase Security. Financial privacy intersects with this topic — explore Bitcoin Plausible Deniability: Wallet Tricks.
Financial privacy intersects with this topic — explore Bitcoin Privacy Economics: Cost-Benefit.
Privacy considerations are covered in Verify Bitcoin Holdings: Privacy Methods.
Privacy considerations are covered in Bitcoin UTXO Privacy Management: Full Guide.
For a broader perspective, explore our hardware wallet buying guide guide.
Step-by-Step Guide to Protecting Your Privacy in the Age of Digital Identity Systems
As blockchain technology intersects with digital identity frameworks, Bitcoin users need a clear strategy for maintaining financial privacy while navigating an increasingly identity-centric digital world. This guide provides actionable steps for protecting your sovereignty at each layer of interaction.
Step 1: Understand the digital identity systems being deployed. Governments and institutions are rolling out various digital identity frameworks: the EU’s eIDAS 2.0 regulation requires member states to offer digital identity wallets by 2026, India’s Aadhaar system covers over 1.3 billion people, and various Central Bank Digital Currency (CBDC) proposals include built-in identity verification. Each of these systems creates a digital footprint that, if connected to your financial transactions, eliminates financial privacy. Map out which identity systems apply to your jurisdiction and understand their data-sharing requirements.
Step 2: Separate your digital identity from your Bitcoin activity. The core defense is compartmentalization. Use dedicated devices or operating systems (Tails OS on a USB drive, a dedicated laptop) for Bitcoin-related activity. Do not access Bitcoin wallets from the same browser or device where you log into government identity portals, social media, or email. Each cross-contamination point — a shared IP address, browser fingerprint, or device identifier — creates a potential link between your legal identity and your Bitcoin holdings.
Step 3: Acquire Bitcoin through non-identity-linked channels. KYC exchanges create the strongest link between your identity and your Bitcoin. Non-KYC acquisition methods include: Bisq (decentralized exchange requiring no identity), HodlHodl (peer-to-peer with escrow), RoboSats (Lightning-based P2P over Tor), Bitcoin ATMs below KYC thresholds (check local limits), earning Bitcoin for goods and services, and mining. Each method has different trade-offs in terms of privacy, convenience, premium paid, and counterparty risk. Diversify acquisition methods to avoid over-reliance on any single channel.
Step 4: Run your own Bitcoin infrastructure. Every third-party service you use is a potential identity leak. Run your own Bitcoin full node to validate transactions privately, your own Electrum server (Electrs or Fulcrum) for wallet queries, and your own Lightning node for payment channels. Connect everything through Tor to prevent your ISP from identifying your Bitcoin network activity. Node-in-a-box solutions like Umbrel, RaspiBlitz, or Start9 make self-hosted infrastructure accessible without deep technical expertise.
Step 5: Use privacy-enhancing transaction techniques. Even with non-KYC Bitcoin and self-hosted infrastructure, on-chain transactions leave public traces. Use CoinJoin (through Sparrow Wallet’s Whirlpool or JoinMarket) to break transaction links. Use PayJoin for direct payments where possible, which disguises the payment as a regular transaction. For everyday spending, the Lightning Network provides better transactional privacy than on-chain payments because individual payments are not recorded on the public blockchain.
Step 6: Resist linking Bitcoin to your real-world identity through metadata. Digital identity systems collect more than just financial data. Location data from your phone, IP addresses from your internet connection, purchase patterns from your spending, and communication metadata from messaging apps all create profiles that can be cross-referenced with blockchain data. Use a VPN or Tor for general internet use, avoid discussing your Bitcoin holdings on social media or messaging platforms tied to your real identity, and pay for privacy-sensitive services (VPN subscriptions, domain names, hosting) with Bitcoin or cash.
Step 7: Prepare for scenarios where identity and Bitcoin intersect by necessity. Tax reporting, regulated exchanges, and certain business transactions may require connecting your identity to Bitcoin activity. When this is unavoidable, minimize the exposure: use a dedicated wallet with separate keys for KYC-linked transactions, never send directly between KYC and non-KYC wallets, and maintain strict UTXO segregation between identity-linked and private holdings. Treat any Bitcoin that touches a KYC platform as permanently linked to your identity.
Step 8: Stay informed about CBDC developments and their interaction with Bitcoin. Central Bank Digital Currencies are the most significant threat to financial privacy in the digital identity landscape. CBDCs could enable real-time transaction monitoring, programmable spending restrictions, and mandatory identity verification for all transactions. Understanding CBDC implementations in your jurisdiction helps you assess the urgency of maintaining Bitcoin as a private alternative. The stronger your self-sovereign Bitcoin infrastructure, the more resilient you are against CBDC-driven financial surveillance.
Common Mistakes to Avoid
1. Using the same email or phone number for Bitcoin services and identity-linked accounts. If you register a Bitcoin exchange account, a wallet notification service, or a node monitoring tool with the same email or phone number tied to your government identity, you create a direct link. Use separate email addresses (ProtonMail or Tutanota) created over Tor for any Bitcoin-related accounts, and consider a separate phone number (prepaid SIM purchased with cash) for services requiring phone verification.
2. Posting about Bitcoin holdings or transactions on social media. Public statements about your Bitcoin activity create permanent records that can be cross-referenced with blockchain data. A tweet saying “just bought 0.5 BTC” narrows the search space for chain analysis firms dramatically. Even vague references (“stacking sats,” “HODL”) associated with your real identity alert potential adversaries that you hold Bitcoin and justify targeted surveillance. Maintain strict operational silence about your Bitcoin activity on any platform linked to your real identity.
3. Assuming VPNs provide sufficient privacy for Bitcoin transactions. VPNs shift trust from your ISP to the VPN provider. If the VPN provider logs traffic (many do despite claiming otherwise) or is compelled by law enforcement, your activity is exposed. VPNs also do not prevent browser fingerprinting, WebRTC leaks, or DNS leaks that can identify you. For Bitcoin activity, Tor provides stronger anonymity because no single entity sees both the source and destination of your traffic. Use Tor Browser or a Tor-configured system for all Bitcoin web interactions.
4. Relying solely on pseudonymity without technical privacy measures. Bitcoin addresses are pseudonymous, not anonymous. Without CoinJoin, Lightning Network, or other privacy tools, chain analysis can trace transaction flows and cluster addresses belonging to the same entity. Pseudonymity is a starting point, not a destination. Layer technical privacy measures (CoinJoin, Lightning, Tor, own node) on top of pseudonymous addresses to achieve meaningful privacy against sophisticated adversaries.
5. Ignoring physical security in your privacy model. Digital privacy measures are irrelevant if someone can physically access your devices. A confiscated laptop with wallet files, a phone with exchange app login credentials, or a visible hardware wallet all compromise your privacy. Use full-disk encryption on all devices, strong device PINs, and hardware wallet PINs. Store hardware wallets inconspicuously. Consider the plausible deniability strategies discussed in our passphrase wallet guide for protection against physical coercion.
Frequently Asked Questions
Can blockchain-based digital identity systems be designed to protect privacy?
Technically, yes. Zero-knowledge proof systems allow identity verification without revealing underlying data — for example, proving you are over 18 without revealing your birthdate. Decentralized identifiers (DIDs) enable self-sovereign identity where users control their own data. However, the implementations being deployed by governments prioritize surveillance capability over privacy. The EU’s eIDAS 2.0, for instance, includes provisions for government-issued digital wallets that create centralized records of identity assertions. The technology can protect privacy, but the political incentives favor surveillance.
How do CBDCs threaten Bitcoin users specifically?
CBDCs threaten Bitcoin users in several ways: mandatory CBDC usage could be tied to exchange regulations, requiring identity verification for any conversion between Bitcoin and the national CBDC. CBDC transaction monitoring could flag users who regularly convert to or from Bitcoin, creating a de facto registry of Bitcoin users. In extreme scenarios, governments could program CBDCs to block transactions to known Bitcoin exchanges or P2P platforms. Having Bitcoin acquired and held outside the identity-linked financial system provides resilience against these scenarios.
Is it possible to be completely anonymous when using Bitcoin?
Complete anonymity is extremely difficult to achieve and maintain, but strong privacy is practical. The realistic goal for most users is unlinkability — preventing any single entity from connecting your real identity to your Bitcoin transactions and holdings. This requires consistent operational security: non-KYC acquisition, own node over Tor, CoinJoin before storage, Lightning for spending, compartmentalized devices, and disciplined metadata hygiene. Perfection is not necessary; each layer of privacy makes surveillance more costly and less reliable for adversaries.
Should I avoid all KYC Bitcoin exchanges?
This depends on your threat model and jurisdiction. KYC exchanges provide convenience, liquidity, and regulatory certainty. For Bitcoin you are comfortable having linked to your identity (perhaps for long-term investment with tax reporting), KYC exchanges are efficient. For Bitcoin you want to keep private, non-KYC channels are necessary. Many users maintain both: a KYC exchange account for their “public” Bitcoin position and non-KYC methods for private holdings, with strict UTXO segregation between the two categories.
Related Resources
- Digital Surveillance and Bitcoin’s Role in Preserving Financial Privacy — Analysis of how expanding surveillance systems increase the importance of Bitcoin’s privacy features.
- CBDCs vs Bitcoin: Political Dynamics and Sovereignty — Deep dive into how CBDC deployment affects Bitcoin’s position as a privacy-preserving alternative to government money.
- Self-Sovereign Bitcoin Infrastructure: Democratizing Node Operation — Guide to building the personal infrastructure that insulates your Bitcoin activity from identity-linked systems.
- Financial Privacy: Anonymous Bitcoin Acquisition Methods — Comprehensive overview of non-KYC acquisition channels that keep your Bitcoin separate from digital identity systems.
- Bitcoin Address Management: Best Practices for Digital Sovereignty — Practical address management techniques that support privacy in an identity-centric digital environment.