The intersection of hardware security and cryptocurrency custody represents one of the most critical yet often overlooked aspects of digital asset security. As computing architectures become increasingly complex, the emergence of sophisticated side-channel attacks has created new vulnerabilities that cryptocurrency holders must understand and address. This analysis explores the broader implications of hardware security for digital asset protection and presents a comprehensive framework for risk mitigation.
The fundamental challenge in cryptocurrency security stems from the dual nature of modern computing systems – they must be both high-performance and secure, yet these goals often conflict. Side-channel attacks exploit the physical implementation of computing systems rather than attacking cryptographic algorithms directly. These attacks analyze patterns in power consumption, electromagnetic emissions, or timing variations to extract sensitive information, including private keys used in cryptocurrency transactions.
The evolution of processor architecture has introduced new attack vectors that weren’t present in earlier, simpler designs. Advanced features like speculative execution, branch prediction, and shared memory spaces – while essential for performance – create subtle information leakage channels that sophisticated attackers can exploit. This presents a particular challenge for cryptocurrency users, as private key operations must be performed on some physical hardware, even if only momentarily during transaction signing.
Modern cryptocurrency security best practices have evolved to address these hardware-level threats through a layered approach. The primary defense is the separation of key storage and transaction signing from general-purpose computing environments. Hardware security modules (HSMs) and purpose-built hardware wallets implement isolated environments where cryptographic operations can occur without exposing sensitive data to the broader system. These devices are designed with specific countermeasures against side-channel attacks, including constant-time operations and power analysis resistance.
The concept of air-gapping has taken on renewed importance in the context of hardware security threats. By maintaining physical separation between internet-connected devices and signing devices, users can significantly reduce their attack surface. This approach acknowledges that while general-purpose computing devices may have unknown vulnerabilities, they can still be used safely as part of a larger security strategy that keeps critical operations isolated.
The role of operational security (OpSec) has expanded to encompass hardware-specific considerations. Users must now think about physical access controls, electromagnetic emissions, and power analysis risks in addition to traditional digital security measures. This has led to the development of comprehensive security protocols that consider both logical and physical attack vectors.
Power Management and Secure Element Vulnerabilities
Power management in hardware security modules represents a complex balance between maintaining secure operations and ensuring consistent device functionality. When hardware wallets experience power-related issues, they are designed to fail securely – defaulting to states that prioritize asset protection over convenience. This security-first approach manifests in various ways, from forcing new authentication attempts to temporarily restricting access to certain functions.
The implementation of secure element chips in modern hardware wallets introduces additional complexity to power management considerations. These specialized microprocessors require stable power delivery to maintain their security features and cryptographic operations. When power levels fall below critical thresholds, secure elements may automatically terminate operations to prevent potential security vulnerabilities that could arise from unstable power conditions. This protective measure ensures that cryptographic operations cannot be compromised through power-related attacks or glitches.
Flash memory and secure element operations require specific voltage thresholds for reliable operation, particularly during critical processes like firmware updates or transaction signing. When power levels become insufficient, devices may exhibit behaviors that appear to indicate hardware failures but are actually protective measures. Understanding these behaviors is crucial for users managing valuable digital assets.
Battery Management as a Security Practice
Battery management represents a crucial aspect of hardware wallet maintenance that directly impacts security and reliability. Regular battery replacement serves not just as a maintenance task but as a critical security practice. Users must understand that battery-related issues can manifest in ways that might initially suggest other hardware problems. Hardware wallet manufacturers implement various strategies to manage low-power situations gracefully, including power monitoring circuits, voltage regulators, and software routines that detect and respond to power-related issues.
Risk Stratification and Defense in Depth
Risk stratification has emerged as a practical approach to balancing security needs with usability. Users can implement different levels of hardware security based on the value of assets being protected and their specific threat model. Small amounts might be reasonably secured on a modern smartphone with hardware security elements, while larger holdings warrant dedicated hardware wallets and air-gapped signing devices.
The future of cryptocurrency hardware security points toward innovative solutions that may help address current vulnerabilities. Open-source hardware initiatives, quantum-resistant cryptography implementations, and novel approaches to secure enclaves are all being developed. Advances in low-power security chips and more efficient power management systems promise to enhance both security and reliability, potentially reducing maintenance requirements while ensuring robust asset protection.
For more on this topic, see our guide on Bitcoin Seed Phrase Security.
For more on this topic, see our guide on MultiSig Backup Maps: Protect Keys and Privacy. Hardware wallet users should also read Hardware Wallet Self-Custody: Full Guide.
For more on this topic, see our guide on Bitcoin Node Hardware: Requirements Guide. For secure signing practices, see Open Source Hardware Wallets: 2026 Analysis.
Hardware wallet users should also read Hardware Wallet Integration: Common Issues.
For secure signing practices, see Hardware Wallet Migration: Script Types.
Step-by-Step Guide to Mitigating Side-Channel Attack Risks
Protecting your hardware wallet against side-channel attacks requires a layered defense strategy that addresses power analysis, electromagnetic emissions, and timing vulnerabilities. This guide provides practical steps for hardening your signing setup.
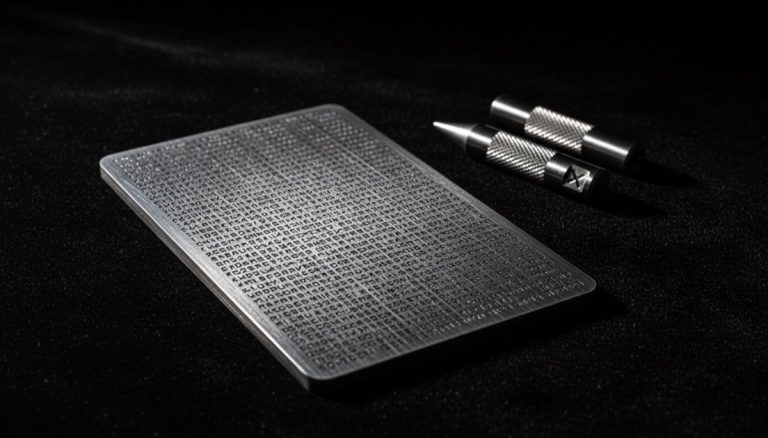
Step 1: Use a dedicated hardware wallet with side-channel countermeasures. Purchase a hardware wallet from a manufacturer that explicitly documents their side-channel protections. Coldcard implements constant-time cryptographic operations and power analysis resistance in its secure element. Trezor uses a randomized PIN entry layout to prevent shoulder-surfing and timing analysis of button presses.
Step 2: Operate in a controlled physical environment. Perform all transaction signing in a private room with no surveillance cameras, smart devices, or other electronic monitoring equipment nearby. Electromagnetic emissions from your hardware wallet during signing operations can theoretically be captured by nearby devices. Maintain at least a two-meter distance from any wireless-capable electronics during signing.
Step 3: Use an air-gapped signing workflow. Disconnect your hardware wallet from USB and use QR codes or microSD cards for transaction data transfer. Air-gapped operation eliminates network-based timing attacks and prevents malicious USB firmware from interfacing with your device. Sign transactions using PSBTs (Partially Signed Bitcoin Transactions) transferred via microSD between your coordinator software and the signing device.
Step 4: Enable anti-phishing and anti-tamper features. Configure your hardware wallet’s anti-phishing measures, such as Coldcard’s login countdown feature and custom display words. These features help you detect if the device has been swapped or its firmware replaced with a malicious version that could exfiltrate keys through covert side channels.
Step 5: Maintain firmware at the latest stable version. Side-channel vulnerabilities are discovered and patched through ongoing security research. Update your hardware wallet firmware when the manufacturer releases security patches. Always verify firmware update authenticity through the manufacturer’s signing key before installing, and maintain a seed phrase backup before any firmware update.
Step 6: Implement a multi-signature setup for high-value holdings. Multi-signature configurations (e.g., 2-of-3) require compromising multiple independent hardware devices to steal funds. Even if an attacker successfully extracts one key through a side-channel attack on one device, they cannot move funds without the additional required signatures from separate devices.
Step 7: Rotate signing devices periodically. For high-security setups, consider migrating to new hardware wallet models as they become available with improved side-channel protections. Transfer funds to new wallets generated on updated hardware and securely dispose of old devices by wiping them and physically destroying the secure element chip.
Step 8: Monitor security advisories and research publications. Follow hardware wallet manufacturers’ security bulletins and academic publications on hardware security. Subscribe to mailing lists like Bitcoin-dev and hardware wallet manufacturer blogs to stay informed about newly discovered attack vectors and recommended mitigations.
Common Mistakes to Avoid
Signing transactions on general-purpose computers. Software wallets running on laptops or desktops are highly vulnerable to side-channel attacks because general-purpose processors are not designed with cryptographic isolation. Speculative execution attacks like Spectre and Meltdown can potentially extract private keys from software wallet processes. Always use dedicated hardware signing devices for any meaningful amount of bitcoin.
Ignoring physical access security. Many side-channel attacks require physical proximity to the target device. Leaving your hardware wallet unattended in accessible locations — at work, in hotel rooms, or in checked luggage — gives an attacker the opportunity to install probes, swap the device, or perform close-range electromagnetic analysis. Treat your hardware wallet with the same physical security as a high-value key.
Disabling security features for convenience. Some users disable PIN protection, auto-lock timeouts, or firmware verification to speed up their workflow. Each of these features serves as a layer in the defense-in-depth model against side-channel and physical attacks. Disabling any single layer reduces the overall security posture of your setup.
Using untested USB cables or power sources. Modified USB cables can contain embedded microcontrollers that intercept data or inject malicious commands. Use only cables from trusted sources, or better yet, eliminate cable connections entirely by using air-gapped communication methods.
Frequently Asked Questions
Can side-channel attacks steal my seed phrase remotely?
Traditional side-channel attacks require physical proximity — typically within a few meters — to capture power consumption patterns or electromagnetic emissions. Remote side-channel attacks do exist (e.g., timing attacks over network connections), but hardware wallets mitigate these by operating offline or through minimal communication interfaces. Air-gapped wallets are effectively immune to remote side-channel attacks since they have no network connection.
Are secure elements immune to side-channel attacks?
Secure elements are designed with specific countermeasures against side-channel attacks, including noise injection, randomized execution, and shielded power delivery. While they are significantly more resistant than general-purpose microcontrollers, no hardware is theoretically immune. State-level attackers with advanced equipment and lab facilities have demonstrated successful attacks on certain secure element models, though the cost and expertise required make this impractical for most threat models.
How does multi-signature protect against side-channel attacks?
Multi-signature requires multiple independent keys to authorize a transaction. An attacker performing a side-channel attack on one hardware wallet would only obtain one key — insufficient to move funds in a 2-of-3 or 3-of-5 configuration. The attacker would need to independently compromise multiple devices, ideally from different manufacturers with different hardware architectures, making the overall attack exponentially more difficult.
Should I worry about the “Dark Skippy” attack?
The Dark Skippy attack exploits malicious firmware that leaks private key material through biased nonce generation during transaction signing. This is mitigated by using open-source firmware from reputable manufacturers, verifying firmware signatures, and employing anti-exfiltration signing protocols. Multi-signature setups provide additional protection because a single compromised device cannot unilaterally sign transactions.